April 30, 2016 Good news regarding ATMs hacked to include skimmers: Operators are finding and fixing them faster. The bad news? Crooks hacked five times more ATMs in 2015 than they did in 2014. Story Tweet
April 30, 2016 Update to “Coin Counting – Their Way” Getting your coins counted by a bank? Are those bank counters accurate? Machines at multiple locations of this bank were short by as much as $50 being 15% of the deposit. Maybe you should test yours? A filed complaint seeks class action status and trial by jury. This Update Start of the Story Tweet
Here are several stories on malware running rampant. It appears that the days of stable software and safe browsing are but faded memories and our future is patches, updates, patches, more patches and more updates, then patches for the holes in the patches and updates.
April 30, 2016 Radio controlled toy maker Maisto ran a web site under Joomla that was lacking multiple security updates. They were hacked to serve the Angler exploit to visitors as the first step toward ransomware. No joy in that toy. Story Tweet
April 30, 2016 Android Users! Be aware of a text message delivered via SMS containing a valid domain name and a subdomain compromised with very bad malware. Story Tweet
April 30, 2016 Water & Electric utility slammed with new malware despite anti-virus software. Story Tweet
April 30, 2016 12 million computers around the world have been installed with “benign”software, yet it is capable of decidedly hostile action. If you bought a computer since 2014 in Australia, France, Japan, New Zealand, Spain, the United Kingdom or the United States, have something called OneSoftPerDay or a Wizz-(anything) running, read the article. Story Tweet
April 29, 2016 SWIFT inter-bank money transfer systems now reporting other breaches similar to Bangladesh. Now they tell us? This Update Start of the Story Tweet
April 28, 2016 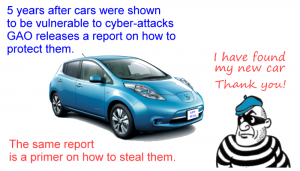 Five years after being shown that modern cars present numerous attack surfaces, the GAO publishes a report to help protect cars from cybersecurity failures. Problem is the same report is a primer on how to hack cars that have an order of magnitude more lines of code than a modern airliner. Story Tweet
Five years after being shown that modern cars present numerous attack surfaces, the GAO publishes a report to help protect cars from cybersecurity failures. Problem is the same report is a primer on how to hack cars that have an order of magnitude more lines of code than a modern airliner. Story Tweet
April 28, 2016 Half a dozen stories:
To its members, the American Dental Association mailed mini-USB drives with new dental billing codes. For a lucky few, something extra, malware! Story Tweet
Perhaps the worst nightmare of any cyber-security specialist, malware found in rod movement computers at a nuclear power plant. Story Tweet
Do repeated Windows 10 update reminders interrupt your work? Not like this! Story Tweet
Microsoft’s hotpatching has been perverted to hide malware. Story Tweet
A Qatar bank was hacked and quite a bit was exposed. Story Tweet
April 27, 2016  Minecraft “LifeBoat” hacked and leaks 7 million records. Check to see if you were exposed. Story Tweet
Minecraft “LifeBoat” hacked and leaks 7 million records. Check to see if you were exposed. Story Tweet
April 27, 2016 150+ verified .GOV email addresses are on the “Beautiful People” dating web site, breached late last year. You tax dollar$ at work. Story Tweet
April 27, 2016  FBI reveals iPhone vulnerability to Apple, nine months after Apple already fixed it. This Update Start of the story Tweet
FBI reveals iPhone vulnerability to Apple, nine months after Apple already fixed it. This Update Start of the story Tweet
April 26, 2016 4th Circuit Court of Appeals just clarified the scope of commercial general liability insurance as regards some cyber-problems. Story Tweet
April 26, 2016 Users say Spotify was recently hacked. Company says, ah, no. Users report changes to accounts. Company says, ah, no. Story Tweet
April 25, 2016  Mexican voter database with over 90 million records taken off Amazon Cloud EIGHT DAYS after discovery and being reported. The database had no password or authentication protection. This update Start of the Story Tweet
Mexican voter database with over 90 million records taken off Amazon Cloud EIGHT DAYS after discovery and being reported. The database had no password or authentication protection. This update Start of the Story Tweet
April 25, 2016 Ashley Madison Class action conundrum: Judge rules plaintiff’s don’t warrant protective anonymity. This update Start of the Story Tweet
April 25, 2016 How a hacked messaging application almost cost the Bangladesh Bank a billion dollars. This Update Start of the Story Tweet
April 25, 2016 20+ million charge cards are available in this one card selling shop and there is almost no media outcry? Do we not care anymore? Story Tweet
April 25, 2016 Why go to the trouble of creating cyber-mischief when you ca get paid hundreds of thousands of dollars for just saying you will? Story Tweet
April 24, 2016 ”Restricted” keys marked “Do Not Replicate” now now be 3D printed thanks to public patent information. Story Tweet
April 23, 2016 Army communications unit criticized for weak cyber-security over several years, already deployed in war zones and cost $12 billion dollars. Don’t our troops deserve better? Story Tweet
April 22, 2016 Does the Windows 10 Blue Screen of Death offer up a Quick-Response (QR) code? Are you sure that code came from the operating system? Will scanning it infect your phone? Be vigilant. Story Tweet
April 22, 2016 Mac Users! RansomWhere monitors your system for ransomware in operation and stops it in its tracks. No-charge to stop crooks! Story Tweet
April 22, 2016 Sadism in malware. As if being infected with ransomware isn’t enough of a strain now comes a variant that displays material to horrify you. The good news? The programmers were not as smart as they were cruel and a no-charge fix is available. Story Tweet
April 22, 2016 Is your website valuable? If not, skip this. If so, then know a web hosting company accidentally erased a very small percent of its servers. Little comfort if you were one of the hundreds to thousands of users on those 60+ machines. How to get more security? Story Tweet
April 22, 2016 Why hack? For the thrills? For extortion? How about as a social statement to expose tools of a surveillance state? Meet “Phineas Fisher”. Story Tweet
April 21, 2016  FBI paid hacker for access to San Bernardino iPhone and won’t tell Apple how it was done. Story Tweet
FBI paid hacker for access to San Bernardino iPhone and won’t tell Apple how it was done. Story Tweet
April 21, 2016  The wheels of justice often grind slowly, but sometimes Lady Justice just swings for the fence. Multiple legal and regulatory decisions were made in favor of consumers to provide a course to redress wrongs and move protecting personal information closer to the forefront of business thinking. Story Tweet
The wheels of justice often grind slowly, but sometimes Lady Justice just swings for the fence. Multiple legal and regulatory decisions were made in favor of consumers to provide a course to redress wrongs and move protecting personal information closer to the forefront of business thinking. Story Tweet
April 20, 2016 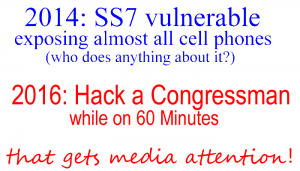 Cell phone vulnerability made public in 2014 was used to hack a US Congressman on 2016. Why is this still a problem? What can you do to protect yourself? Story Tweet
Cell phone vulnerability made public in 2014 was used to hack a US Congressman on 2016. Why is this still a problem? What can you do to protect yourself? Story Tweet
April 19, 2016 Ransomware via resumes, a cautionary tale for applicants and companies alike. Story Tweet
April 18, 2016  Some excellent cyber security education was classified in 1970. Nothing secret, just to “control dissemination”. Might have saved a lot of grief if it had been part of the education curriculum. Story Tweet
Some excellent cyber security education was classified in 1970. Nothing secret, just to “control dissemination”. Might have saved a lot of grief if it had been part of the education curriculum. Story Tweet
April 18, 2016 GozNym may be the Borg of banking trojans. This hybrid has successfully taken millions from 24+ banks in the US and Canada. Story Tweet
April 18, 2016  Two new critical vulnerabilities found in QuickTime after Apple stops delivering security upgrades. According to US-CERT time for that application to go. Story Tweet
Two new critical vulnerabilities found in QuickTime after Apple stops delivering security upgrades. According to US-CERT time for that application to go. Story Tweet
April 18, 2016  Drone strikes Airbus. Deploy the eagles. Story Tweet
Drone strikes Airbus. Deploy the eagles. Story Tweet
April 17, 2016 RCMP had global BlackBerry key for all non-corporate users since 2010. How did they get it? Do they still have it? Who else has it? Is BlackBerry secure or not? This Update Start of the story Tweet
April 17, 2016 Two more on the DOJ/FBI vs Apple situation. What was on the San Bernardino cell phone? Apparently nothing of value. Tin-foil-hat-wearing person called that one right last month. Story Tweet So who actually cracked what? Reputable source says it wasn’t Cellebrite. Some questions answered, but those answers raise more questions? Story Tweet One thing is certain, this event has cost a lot in money and bad press. Start of the Story
April 16, 2016 Scorecards on the cyber security efforts for federal, state and local governments. Some good, most less so. Story Tweet
April 16, 2016 Uber reported on 12+ million trips to regulators during just the last six months of 2015. Their new warrant canary is still singing. Story Tweet
April 16, 2016  US House of Representatives, Judiciary Committee, is working on restricting mandatory arbitration clauses. This would move cases from a lopsided private system to a public legal system where there is equal justice under law. Story Tweet
US House of Representatives, Judiciary Committee, is working on restricting mandatory arbitration clauses. This would move cases from a lopsided private system to a public legal system where there is equal justice under law. Story Tweet
April 15, 2016  US Senate proposes to ban core elements of cyber security. Think the crooks will obey the law? Story Tweet
US Senate proposes to ban core elements of cyber security. Think the crooks will obey the law? Story Tweet
Update: The proposed version is worse that last week’s draft. In some cases, much worse. This Update Tweet
April 15, 2016 Update to 3/27/2015 re reported hacking of law firms. This Update about why Start of the Story Tweet See also the Panama Papers
April 15, 2016 Use Bit.Ly or other URL shorteners? Beware! Those can make data you think safe get gone in 60 seconds. Story Tweet
April 15, 2016 You have a home router. You might know it or not. What you probably don’t know is that your cell phone can infect it and next time you think you’re going to “MyBank” you’ll actually be at “TheirBank” happily disgorging your userid and credentials. You can stop it with some simple steps. Story Tweet
April 15, 2016 Microsoft objects to indefinate duration gag orders citing “Freedom of Speech” as defined by the First Amendment. Story Tweet
April 15, 2016 New Jersey and Maryland public transit are listening on passsenger conversations. Is there an expectation of privacy? Who listens to all that chatter? Story Tweet
April 14, 2016 Tweet1 Tweet2 Two updates on the FBI vs Encryption The San Bernardino crack won’t work on 5S or later iPhones, but the device is becoming less of a worry than end-to-end encryption service. What did it cost for the SB crack vs the DOJ legal expenses? Story Since 2002 dealing with encryption has been on the FBI radar, but not always in its mandatory reports. Some attempts at imposing laws appeared to be based on a presumption of not(innocent). Story
April 14, 2016 Former employee leaves on Friday with personal storage device containing information on 44,000 people. What information? FDIC isn’t saying. Story Tweet
April 14, 2016  Retro-malware “Petya” cracked by security researchers. Step-by-step removal possible without paying ransom. This Update Start of the Story Tweet
Retro-malware “Petya” cracked by security researchers. Step-by-step removal possible without paying ransom. This Update Start of the Story Tweet
April 14, 2016 Malicious advertising (malvertising) hits almost 300 sites in the Netherlands. One site alone has 50 million visitors a month. How many were infected? Who is responsible if users lower their adblockers? Story Tweet
April 12, 2016 Multiple stories for your information. Tweet
Five all-too-common cyber-security myths we need to overcome much sooner than later. Story
Latest security report from Symantec. Crooks getting smarter, incidents are increasing in frequency and severity, reporting is shrinking and we should all be more cyber-worried. Story
Anti-surveillance technique used by terrorists … and the director of the FBI. Could you be harboring this tool in your home or office? Story
What goes around comes around. Judge orders FBI to release exploit code used to compromise the TOR browser. They are resisting disclosure. Story
Just because it is found on the internet does not make it true or accurate. Just ask the residents of a small place not too far from the US center who have been visited by the FBI, IRS, USMS, police, and angry people. Or, the family in Atlanta that appears to be where lost cell phone call home. Story
Facebookers – a scam is targeted directly at YOU! That notice about “your account is suspended” may be a scam. Read this to recognize it and do not, Not, NOT click on the link provided. Story
Shodan, the search engine for the internet-of-everything, found some radio stations that were not secured. The stations were hacked to broadcast a … furry … podcast and the station engineers were locked out for about 90 minutes. Story
April 11, 2016  Senate bill would ban all but hackable encryption for us. Story Tweet
Senate bill would ban all but hackable encryption for us. Story Tweet
April 11, 2016  Irony bites, sometimes very hard. You want a security video camera, research and get one from the world’s largest web-based retailer and get something extra, decidedly the opposite of security. Story Tweet
Irony bites, sometimes very hard. You want a security video camera, research and get one from the world’s largest web-based retailer and get something extra, decidedly the opposite of security. Story Tweet
April 10, 2016 UK hacks the most vulnerable, not suspected of anything, just because it is legal? Story Tweet
April 10, 2016 Part of the voter database in the Philippines was hacked and posted on line. “Officials” said nothing of importance was taken. How about personally identifiable information (PII) and fingerprints for over a million voters? Story Tweet
April 8, 2016 Update to February 2015 breach that exposed 80 million. Anthem tries a rare tactic and the judge has a succinct response. This Update Start of the Story Tweet
April 8, 2016 Doing business on eBay? 7 reasons to be cyber-worried. Story Tweet
April 7, 2016  Social media delivers 18% of the malware at work. Get rid of it? Not so fast. Business use social media too. Now what? Story Tweet
Social media delivers 18% of the malware at work. Get rid of it? Not so fast. Business use social media too. Now what? Story Tweet
April 7, 2016 Chrome browser extensions highjacked to display advertising page before showing desired page. Tracked users too. Story Tweet
April 7, 2016 Poor security irks hacker so much he takes data and posts it on the Dark Web. Or did he? Story Tweet
April 7, 2016 ComEd in northern Illinois is moving forward with electronic billing (good) sending information in unprotected PDFs containing personally identifiable information (bad). Story Tweet
April 6, 2016 Update: Panama Papers: lawyers gave interview the week before the huge public exposure. One may have brought increased regulatory attention on them. Story Tweet
April 6, 2016 Sick of Win10 adware? Afraid you’ll click the wrong icon and get a brick where you used to have a computer? Happy with what you’ve got? Don’t want to mess with the registry, scripts, tweaks, etc? Consider GRC/Never10 application from all-round good guy, Steve Gibson. Story Tweet
April 6, 2016 Meet “Petya”, retro malware that screws up new technology in a way that even the crooks can’t unscramble. Don’t even think about paying for this extortion. Story Tweet
April 6, 2016 Got an iPhone 6S or 6S+ running iOS 9.2 to 9.3.1? If so, then anyone who has physical access can bypass your lock screen. You can stop this exploit. Story Tweet
April 6, 2016 Microsoft main authentication for Outlook, Azure and Office had a serious vulnerability found by a bounty hunter. Good news: it has been fixed. Better news: It only cost $13k in bounty. Bad news: How did it get past all the internal checking in the first place? Story Tweet
April 5, 2016 Update  Panama Papers draws first blood. Iceland Prime Minister resigns. May have evaded disclosing conflict of interest in shell company. This Update Start of the Story Flash Tweet
Panama Papers draws first blood. Iceland Prime Minister resigns. May have evaded disclosing conflict of interest in shell company. This Update Start of the Story Flash Tweet
April 5, 2016  Panama Papers Updates: Paper? Nah, electrons! Following the post-hack script (psst, that is the wrong one!). What may have started the breach. This Update Start of the Story Tweet
Panama Papers Updates: Paper? Nah, electrons! Following the post-hack script (psst, that is the wrong one!). What may have started the breach. This Update Start of the Story Tweet
April 5, 2016 Truecaller anti-telemarketing call / anti-spam text tool had a weakness that could expose the personal information for 100 million users. Updates available. Story Tweet
April 5, 2016 Reddit Canary stopped singing 3/31/2016. What? Story Tweet
April 5, 2016 US/Canada alert on influx of ransomware. 7 steps to help prevent getting it and 1 step on if you do. Story Tweet
April 5, 2016 US Government files hacked for YEARS according to FBI Alert. “We’re screwed”. Story Tweet
April 4, 2016  The Panama Papers may rock the world like the Pentagon Papers, or CableGate from WikiLeaks, but at its core it is a huge breach in the electronic records of a law firm. Story Tweet
The Panama Papers may rock the world like the Pentagon Papers, or CableGate from WikiLeaks, but at its core it is a huge breach in the electronic records of a law firm. Story Tweet
April 4, 2016  Trump Hotels breached … again. Story Flash Tweet Tweet
Trump Hotels breached … again. Story Flash Tweet Tweet
April 4, 2016 49.6 million records exposed Turkish citizens name, national ID number and more. Story Tweet
April 4, 2016 You were speeding so you’re not really surprised you got a ticket, a nice new eTicket, just click here to pay. WRONG! New scam with a new twist. Story Tweet
April 3, 2016 Your vote counts, right? Would you believe half a dozen elections not far from the USA were stolen? Could it happen here? Read the epiphany that started it. Story Tweet
April 3, 2016 Political fallout from failed communications security may sink the 86 billion Euro Greek bailout. Are you taking communications security for granted? Story Tweet
April 3, 2016 Counter-fraud activities at the federal and state levels slow tax return processing. Story Tweet
April 2, 2016  That $100 bill you have. Printed in the US or Peru? You might be surprised and not necessarily in a good way. Story Tweet
That $100 bill you have. Printed in the US or Peru? You might be surprised and not necessarily in a good way. Story Tweet
April 2, 2016 (From late March) Medstar hospital system attacked and reverts to 1970s-era record keeping for which they were unprepared. Story Update It is ransomware.
April 2, 2016 More variants of malware for point-of-sale terminals. Story
April 2, 2016 Apple update exposes users to a hack so severe it allows access to places even ‘root’ isn’t allowed. Story Tweet
April 2, 2016 Deep Dive into Joker’s Stash. A long look at a place where you can buy thousands, tens of thousands, of charge cards and more. Story Tweet
April 2, 2016 End of an Epoch! As of 6/1 there won’t be an Internet anymore. What will replace it? The internet. AP Style guide drops the proper noun capitalization. Story Tweet
April 2, 2016 Invest $40 in hardware and hack a $28k Police Drone from two kilometers away. How? To start for $28k all you get is deprecated WEP security. Story Tweet
April 1, 2016 March clean up – items of information that were gathered but not published in time. Tweet
Apple is building its own network servers to enhance security. The need for security is understood, but why build your own? They have a good reason. Story
Your company has been breached. What are your responsibilities in your state and for the states of those affected? Story
Gaming the lottery in Connecticut, but not the way they had in mind. Story
Great webinars each day for a week, but scheduled for UK time. Now available on line thanks to Sophos. Story
The value of a thing is the cash it will bring. So how much does a charge card number bring? A set of personally identifiable information? An Uber account? Story
You get an email from a domain ending in .gov. Do you trust it or is it a scam? How some bad programming in some government web sites and a popular URL shortening tool is allowing crooks to reach more victims. Story
How secure are Presidential campaign websites? Which is more secure than another? Story
How CNBC gave a great lesson in internet security by sharing user-supplied credentials with advertisers and other services. Story