Compromises in 2016 affecting an unknown number
2016 Compromises affecting 10,000 or more
2016 Compromises affecting less than 10,000
2016 Summary of Compromises
2016 General Information
01/01/2016 Cyberoam
A security researcher found Cyberoam database for sale at 100 bitcoins, about $43,000. Compromised information included names, phone numbers, email addresses, and some transaction details. Also exposed were Cyberoam partner information. The company was made aware of the information for sale in late December and took a week to confirm the exposure.
There is a conflict as to what was exposed. Cyberoam CEO Hemal Patel told BusinessLine: “We have informed our partners and customers of a cyber-attack aimed at a web service in the Cyberoam.com domain via a publicly-accessible read-only API. We have taken steps to mitigate any exposure, and a thorough investigation is ongoing. Initial analysis indicates that the potentially exposed data consists of a marketing database from the year 2012 as well as some publicly available information and other non-sensitive information,” The security researcher insists the data was a marketing database and the company’s entire customer and partner database with over one million records. Cyberoam was acquired by UK security firm Sophos in early 2014 (press release).
01/05/2016 Linode
Today Linode, a virtual private server provider based Galloway, New Jersey announced they were resetting all credentials because …
A security investigation into the unauthorized login of three accounts has led us to the discovery of two Linode.com user credentials on an external machine. This implies user credentials could have been read from our database, either offline or on, at some point. The user table contains usernames, email addresses, securely hashed passwords and encrypted two-factor seeds. The resetting of your password will invalidate the old credentials.
Linode has not had a Happy New Year. Starting Christmas they were victims of a DDoS attack that wasn’t mostly contained until early 1/04/2016. Problems remain.
1/06/2016 Child buys own present
with Dad’s iPad & Apple ID
A seven year old child was playing Apple iTunes’ Jurassic World and wanted a snazzier dinosaur. So he used Dino Bucks to buy one. Actually he bought quite a few. In the five days between 13 and 18 December the child made 65 purchases from Apple. Dino Bucks are backed by real funds and dad’s linked charge card took a hit to the tune of almost $6,000.
Apple has had problems before making it easy for kids to spend real money via in-app purchases. In early January 2014 Apple paid over $30 million to settle (without judgment) charges from the Federal Trade Commission (FTC). In September 2014 another $19 million was paid (again, a settlement, not a judgment) by Google to the FTC for the same problems. Still, there is plenty of responsibility to share and some questions. How do you return a snazzy dinosaur? More at Sophos
[ How many others were affected? Read Things Kids Games Do that they Might Not Tell You March 2013 Federal Trade Commission (FTC) -ed ]
1/10/2016 Banking Trojans on the rise
Japan hit by Rovnix, other trojans abound
This advanced banking trojan starts like many others with a fake email and an attachment. It might be for a package delivery or an invoice, any social engineering to compel the recipient to open what appears to be a .ZIP attachment. From there the Rovnix downloader is launched and the malware installed.
The login pages for at least a dozen Japanese banks are modified so the trojan becomes the man-in-the-middle and captures the login and security replies whenever the consumer accesses their bank. In some instances the malware asks the consumer to download new smartphone applications which, unfortunately, compromise smartphone based two-factor authentication. The level of language and social preparedness makes this a major threat. Of 54 antivirus suites tested only 4, less than 8%, caught Rovnix by name. Some others caught it as a “Generic Trojan”.
Banking trojans Dyre (25%), 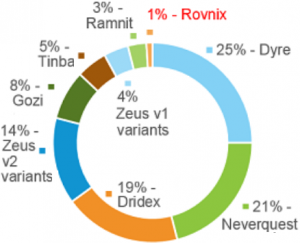 Neverquest (21%), and Dridex (19%) make up 65% of the known banking malware in use. Zeus V1 and V2 are another 18%. Rovnix is 1%, but given its sophistication, is expected to expand.
Neverquest (21%), and Dridex (19%) make up 65% of the known banking malware in use. Zeus V1 and V2 are another 18%. Rovnix is 1%, but given its sophistication, is expected to expand.
How many were affected? No one knows! Sources: IBM Security Intelligence and TheRegister/UK
[ chart from IBM. Related
Cridex, ZeuS, now Dridex from January 2015. Dyre masquerading as Google Update Services from June 2015. Is that your bank calling you? from October 2015. Dyre Just in time for the holidays from November 2015. -ed ]
1/11/2016 Is your smartwatch working for someone else?
Think on this for a minute. Your smartwatch contains microaccelerometers and other sensors to measure with great precision how your hand is moving. What can that say about you, say during the time when you are entering your personal identification number at an ATM? How about your other wearable technology?
The security of Wearable Wristband and Armband Devices (WADs) such as smartwatches and fitness trackers is of great concern not directly because of the device itself being exploitable but because of the very nature of wearable devices being wearable. A smartwatch is indeed potentially worn for an extended period such as the whole day, offering a pervasive attack surface to cyber-criminals [ from the introduction, highlighting ours – ed ]
… implementation presented in this research can perform touchlogging and keylogging on 12-keys keypads with above-average accuracy even when confronted with raw unprocessed data. Thus demonstrating that deep neural networks are capable of making keystroke inference attacks based on motion sensors easier to achieve by removing the need for non-trivial pre-processing pipelines and carefully engineered feature extraction strategies. Our results suggest that the complete technological ecosystem of a user can be compromised when a wearable wristband device is worn. [ from the summary, highlighting ours -ed ] ( Source summary and 125 page PDF no registration required for download)
The above is from a research paper that demonstrates that your wearable tech could indeed, be working for someone else. There is a simple starting countermeasure, wear your WAD on your non dominant hand. There are some more on study page 84. More on the story at Sophos. How many have already been affected by this? No one knows!
2/04/2016 Update Smartwatches
Every Step You Fake: A Comparative Analysis of Fitness Tracker Privacy and Security from Open Effect, a Canadian non-profit organization. The smartwatch apps installed gave up usernames and passwords and were vulnerable to being packed with incorrect data which opens users to becoming victims or faking figures to lower insurance rates. More from RT.
7/25/2016 Update Smartwatches/Fitness Trackers vs ATM
Smartwatchs or Fitness Trackers can hack your ATM by using a “Backward PIN-Sequence Inference” algorithm to capture slight hand movements while typing or entering ATM passwords. Easy way to avoid this problem? Use the hand without the device. More at The Hacker News
1/11/2016 Locking your files for fun & profit
A new variant of CryptoWall called version 4 is nastier, but also preventable.
For a good review of the current version and how to prevent problems like it see this Sophos article. There are many tools for prevention. In email don’t open attachments you are not expecting unless you have a sandbox, and maybe not even then. In websurfing use real time anti-virus protection. For your existing files run scanners. For highly valued data there is just one preventative measure: backup, Backup, and BACKUP. Use multiple media at intervals proportional to your risk aversion How many have been infected by this? No one knows!
[ on the main machine where significant efforts are expended frequently I backup the work directory to another machine several times a day. Over the wire takes about ten minutes so I do it when I take a break. That other machine is backed up at least once a week, often more frequently. There are a dozen media in rotation. The backup media are not connected to the machine. This air-gap means the virus can’t reach them to contaminate them. If malware gets me, even if was dormant for a week, the majority of material will survive. Is that enough? Maybe, but not all ransomware follows through on unlocking even after you pay. Further, is your machine really clean of the virus or have they made a note to revisit you in a few months? Read what Rudyard Kipling, Nobel Laureate in Literature in 1907, wrote circa 1911 about paying tribute. See also this guide from Comparitech on how to prevent & remove ransomware -ed ]
1/12/2016 Update Ransomware underreporting
Increases of 50% in some nations are not making into the major media. Why? “Face” is lost because some crook managed to infiltrate your systems and access all of the information you tried to protect. More at DataBreachToday
1/14/2016 Update Cloud data vulnerable
A company used computers at their site all of which were mapped to drives on the cloud. Then someone opened an email and opened the “invoice” attachment. Over 4,000 files on the cloud drive were encrypted and held for ransom. The company was fortunate that the problem occurred just prior to holiday down time and well-prepared in that they had a backup, not connected to their systems. See [ comments ] above for more recommendations. Be prepared and why not to pay the ransom. Source:KrebsOnSecurity
1/11/2016 Blackberry PGP phones cracked
Using forensics software made by Cellebrite, Netherlands Forensic Institute (NFI) has reported they can read encrypted messages sent via PGP BlackBerry phones using encrypted email. Neither the Federal Bureau of Investigation nor Drug Enforcement Administration would make a substantive comment. The DEA wrote “I’m afraid I can’t comment on your question. As I’m sure you can appreciate, confirming or denying this capability provides information on tactics, techniques and procedures that we can’t discuss.”
John Chen, Blackberry Ltd. CEO, wrote that “privacy and security form the crux of everything we do. However, our privacy commitment does not extend to criminals.” BlackBerry does not sell devices with PGP. Those are sold by customizers. Sources: Motherboard/VICE and NakedSecurity/Sophos.
1/12/2016 Update: RCMP can too, as far back as 2011
A court case (see paragraphs [10] – [13]) indicates that the Royal Canadian Mounted Police (RCMP) have the capability to recover these Blackberry PGP encrypted messages. From another case comes “[58] Four of the Blackberries seized on November 23, 2011 contained encrypted data through subscriptions to a service called “Pretty Good Privacy” or PGP. Three of the Blackberries were analyzed by the RCMP’s Technical Assistance Team in Ottawa and the contents were decrypted and reports prepared.” [ bolding ours – ed ] Source
4/15/2016 Update: RCMP had the global key!
see Cell Skimmers 4/15/2016 Update.
1/15/2016 Update: New York wants back doors
The New York state assembly has a proposed bill (2 page PDF) that would ban encrypted mobile phones and impose a fine of $2,500 per phone sold in New York that does not have a security bypass. Interestingly the Netherlands opposes backdoors. So does Apple. So does Blackberry even when it got them tossed out of a whole country market. Read more at NakedSecurity/Sophos
1/16/2016 Update: France: Backdoor? Non!
The pro and con of “strong” security
Pro: we (non-technical, even thumb fingered, civilians) can prevent bad people from our information and information we have for others, including our customers. We can avoid being a victim of stolen emails, texts, highjacked browser history, being tracked by location data, and much more. Using it is protection, just like the lock on our home, but in our cell phones. Con: Genuinely good secure protection (including strong encryption) makes it more difficult for intelligence services and law enforcement.
One offered compromise is a door with a spare key, just for them. Sometimes held by a third party as a safeguard. Both points of view carry the catch phrase “if we don’t do as we say the bad guys win”. Is there a “right” answer? The sides are shaping up and there is no easy grouping.
In the con camp: Some political groups, including the United Kingdom and the State of New York are against strong encryption. In the pro camp: A lot of technology groups including Apple, Facebook, Blackberry, Google, Microsoft, Twitter and Yahoo. Also some other political groups including the Netherlands and, as of last Thursday, France joined the club, rejecting backdoors and essentially calling the weakening of security … a bad idea. (announcement in French) More see NakedSecurity/Sophos
1/17/2016 Update: Blackberry says
In an unsigned blog post Blackberry wrote that their devices were as secure as they have always been. It may be that the PGP application (not created by Blackberry) was cracked. Because law enforcement isn’t saying, Blackberry has a hard time fighting for its reputation. The cases lack details, saying only the messages were extracted. More at NakedSecurity/Sophos
1/28/2016 Update: Maybe not the phone
PGP might be pretty good to protect us from us, but not from them.
This thread started with a story that law enforcement can crack Blackberry/PGP communications. The initial updates showed court cases where information was extracted, but the language wasn’t clear. Was the phone cracked or the application? Blackberry claims the phone is fine. This update indicates more that the PGP application is the weak spot.
The exposure starts with a user’s PGP KeyIDs which can be scraped from a message after it has been encrypted. This starts a trail. Using a national level information repository a search can be done for other messages with the same key. Information about an email, but not the contents, are called meta-data and some those may not be encrypted at all. This can provide the route traveled by the message. There is much more at this Motherboard article where Dr. Nicholas Weaver is quoted as saying “PGP is the NSA’s friend”. After watching this Youtube video 19m 55s from USENIX Enigma 2016 you may never trust the internet again.
2/01/2016 Update: Don’t Panic
A counterpoint that the phrase “going dark” may not be accurate in support of “backdoors” to encryption and the general weakening of individual privacy. There are more methods of observing the populace than ever before. See https://nc3.mobi/references/2016-info/#0201 for details.
1/12/2016 Power Grid Damaged
For decades an advanced persistent threat has damaged the US power grid over 600 times. An affiliated group scored an additional 200 incidents of damage. These attacks are tracked by CyberSquirrel1. An odd name for cyber-trackers? Well, the attackers being tracked are squirrels, birds, raccoons, snakes, rats, and beavers. The site allows selection of month, year and critter type and it will display a map and attribution for successful anti-power grid operations. The group’s motto is CyberWarfare4Ever. source
C. Thomas, a strategist at cybersecurity firm Tenable Network Security, wrote in a column published 1/6/2016 in the Christian Science Monitor “Opinion: Squirrels are bigger threat than hackers to US power grid,” The statistics at CyberSquirrel1 would tend to support that opinion. Over 600 since 1987 for squirrels and less than half a dozen for independent or nation-state hackers. [ It might be a few more for the hackers whose exploits against power and other infrastructure isn’t being completely disclosed. -ed ]
1/12/2016 Faux Certificate
Spymel malware is using a DigiCert certificate
The user gets an email with an attachment. The attachment has a digital certificate from a trusted company. The user clicks on it and the Spymel malware watches multiple processes including Task Manager and Process Explorer to log keystrokes revealing user identification and passwords and sending them back to the malware operator. DigiCert has since revoked the certificate, but this latest example shows the fragility of the certificate concept for security. Source [ Was the email expected? From a regular source? Or, was it just “something”? Security is in your hands. How many were infected? No one knows! -ed ]
1/12/2016 Stuxnet Damage Capability for Everyone
Just what we didn’t need, an easy way to damage industrial motors.
There are two well known hacks that damaged industrial equipment. In 2009 the Stuxnet worm caused Iranian centrifuges to shake themselves broken. In 2014 a German steel mill reported a furnace damaged by a hack. Both of these required considerable knowledge of the workings.
The attack plane is a device called a variable frequency drive, an electronically controlled motor. Schneider-Electric, Allen-Bradley, ABB, and Vacon, all makers of these devices, do not require authentication to read or write to the controlling equipment. Worse each controller contains the “max safe speed” giving hackers a target to exceed for damaging effect. These motors are everywhere.
This isn’t a software patch kind of repair repair. The communication protocols are not secure. Enforcing a more secure protocol eliminates backward compatibility with mullions of existing motors. Details and more at Wired. How many of these systems have already been attacked? No one knows!
1/12/2016 Another firewall hacked
Last month an unauthorized backdoor was found to have existed in Juniper security since 2012. Now Fortinet’s FortiGate firewall networking equipment using FortiOS was found to include a “secure shell” (SSH) backdoor allowing access via a hardcoded user name and hardcoded password that existed between November 2012 and July 2014. According Fortinnet this bug was fixed in July 2014, but no advisory was transmitted to its user. The National Vulnerability Database (NVD) for CVE-2014-2216 gave it a CVSS v2 Base Score: 7.5 (HIGH), Impact Subscore: 6.4 (of 10), Exploitability Subscore: 10.0 (of 10), Access Complexity: Low, Authentication: Not required to exploit and described it as Impact Type: Allows unauthorized disclosure of information; Allows unauthorized modification; Allows disruption of service. The details and links to the exploit code are available at TheHackerNews. How many were exposed? No one knows!
1/13/2016 Upate: Fortinet responds/Juniper 3rd flaw
In a blog post, Fortinet claims that “this was not a ‘backdoor’ vulnerability issue but rather a management authentication issue,” and that it was both publicly disclosed and patched in July 2014. Unfortunately for Juniper users another flaw was discovered involving the use of the Dual_EC random-number-generator algorithm, which is known to have been backdoored by the U.S. National Security Agency. Juniper promised to remove this sometime in the future.There is a “war of words” going on between security appliance makers as to whether this was a hack, features gone bad, or compliance with intelligence agencies. None of these are good for the consumer who thought they were buying security. More at DataBreachToday.
1/22/2016 Upate: Fortinet: Other devices affected
Fortinet said the problem was not an intentional backdoor, but “a management feature which relied on an undocumented account with a hard-coded password.” [ umm, isn’t that a back door? -ed ] Last week, the company found that some versions of FortiSwitch, FortiAnalyzer and FortiCache are also affected. Upgrades are advised. See PCWorld. [ these non(backdoor) backdoors have been around for years and were discovered by independent security researchers. How much “just trust us” does this consume? -ed ]
1/12/2016 Popular AntiVirus & Password Manager, hacked
Popular anti-virus software from Trend Micro has a password manager that could be compromised to expose every saved password. An emergency patch has been provided. TrendMicro also uses a self-signed certificate which means that secure hypertext (HTTPS) errors are not provided to the user. How many were exposed? No one knows! More at TheHackerNews.
1/14/2016 Theremostat #NEST #FAIL
There are Inherent Dangers in the Internet of Things and just because we can connect devices does not mean we should. In this case, during the cold night, many (how many no one knows) Nest thermostats drained their batteries and failed. People who were expecting to sleep well were awakened by crying babies or worse. Elders or ill people were affected. What impact does a failed thermostat have on an empty house, in cold weather, with modern plastic piping? What caused the problem? Would you believe an “update”, automatically applied in December 2015? In the cold of January 2016 the devices drained their batteries and went offline while temperatures dropped.
This is not the first time devices to make your lives easier have come back to haunt us. Remote car access: Good-no keys. Bad-crooks can just open the doors with radios. Home security devices: Good-turn off the lights, lock the doors and set the alarm after you leave. Bad-your house won’t let you in, the lights turn themselves on when you’re not home, and every stray cat sets off loud alarms during their nightly visit. More bad-crooks electronically listen as you enter your codes, clone them, then open your doors for themselves. There are many more.
The author (see URL below) notes Nest has an 8,000 word service agreement which “prohibits customers from suing the company or joining a class-action suit. Instead, disputes are settled through arbitration.” See our article and image on that. More at NY Times (no idea why the article is in the fashion section) and read this tweet for a $25 solution to the failing Nest thermometer.
1/14/2016 Long Shadow of Silverlight
A weakness in a very popular browser plug in existed from 2013 to 2016. How many were affected?
In mid 2015 there was an article from ArsTechnica on how discovery of zero-day weaknesses turned into tens of thousands of US dollars for a Russian security researcher and exploit designer. Not all the weaknesses offered for sale in 2013 were purchased.
One that wasn’t referred to a zero-day vulnerability in Silverlight, Microsoft’s plug-in for displaying media and rich interactive applications. It works in multiple browsers in multiple operating systems. Because of its widespread use a compromise of Silverlight could affect many, many, users. The weakness, unknown to Microsoft, could allow remote access allowing theft of information, surveillance and more, all without the user being aware. According to the National Vulnerability Database (NVD) CVE-2016-0034: “Microsoft Silverlight 5 before 5.1.41212.0 mishandles negative offsets during decoding, which allows remote attackers to execute arbitrary code or cause a denial of service (object-header corruption) via a crafted web site, aka Silverlight Runtime Remote Code Execution Vulnerability.” [ highlighting ours -ed ]
Kaspersky Lab was able to find a series of unique string samples in the code that could be used to identify the exploits capitalizing on the weakness. Once identified, attacks against some Kaspersky customers were found to contain some of sample strings. CVE-2016-0034 was patched during “Microsoft Patch Tuesday” on January 12, 2016.
SecureList/Kaspersky blog of 1/13/2016. More on the story from Business-Reporter/UK [ that we have a regular “patch day” is indicative of how well we accept that such flaws exist in the first place. -ed ]
1/15/2016 Your doorbell leaks passwords?
Thanks to PenTestPartners we know The Ring is a Wi-Fi enabled doorbell that allows you to answer the door from your mobile phone. So, you don’t even have to be home to talk to visitors, mail carriers, couriers, etc. It also controls a CCTV camera so you can see as well as talk. Problem is your wifi key is easily exposed. Read more at TheHackerNews.
1/15/2016 Bitcoin Exchange robbed – last year?
Cryptsy robbed in mid-2014.
Cryptocurrency exchange Cryptsy announced today that it was robbed in mid 2014 of 13,000 bitcoins and 300,000 litecoins. On 7/29/2014 BTC was trading at 582.20 for a value at theft of about $7,568,600. Cryptsy traded bitcoins and many other “altcoins”.
Why the delay? They were profitable and used their profits to pay off customers. Profits dropped, incorrect bad press came out, the FBI referred them to the Internet Crime Complaint Center (IC3), there was no reply, and a run started. The exchange has suspended all trades and will file for bankruptcy unless there is a recovery. It appears (see announcement link) that the stolen BTC are still in transfer account so they may be recoverable. How was the theft accomplished? A developer of had placed an IRC backdoor into the code of wallet, which allowed it to collect information to perform and attack. How many were affected? No one knows!
There have been several BTC exchanges that have experienced several operating difficulties. In 2014 Mt. Gox was robbed, apparently by the founder who was arrested in August 2015. See also DataBreachToday
1/17/2016 Headline Hype vs Tolerable Truth
It was reported that a zero-day weaknesses found in the Linux kernel affects 2/3 of all Android devices, millions of servers and desktops. Attackers can execute code or steal data. All true and the sky is falling … a few drops at a time. The hype is overdone.
A little more of the facts: CVE-2016-0728 is shown by Mitre without explanation, just that the vulnerability number has been reserved. The problem lies in 2012 changes that affect the “keyring facility” which encrypts and stores login information, encryption keys and certificates, and making that information available to applications. (source)
A user with lesser privileges can gain the highest access (root level) and do almost anything. For a computer physical access is required. For devices a malicious program could do the same. The full exploit “takes about 30 minutes to run on Intel Core i7-5500 CPU” (from PerceptionPoint, see below). Other protections for computers include Supervisor Mode Execution Protection (SMEP) and Supervisor Mode Access Prevention (SMAP). For devices, including Android based cell phones, the Security-Enhanced Linux (SELinux) is a kernel level module providing security by enforcing access control security policies. So, is there a problem? Yes. Is the sky falling? No. Proper patches provide protection.
Detailed disclosure from PerceptionPoint. Proof of concept code. More … How many were affected? No one knows.
1/19/2016 Update Hype overdone (as we said)
Regarding Android devices:
We believe that no Nexus devices are vulnerable to exploitation by 3rd party applications. Further, devices with Android 5.0 and above are protected, as the Android SELinux policy prevents 3rd party applications from reaching the affected code,” said Adrian Ludwig, Android’s lead security engineer. Also, many devices running Android 4.4 and earlier do not contain the vulnerable code introduced in Linux kernel 3.8, as those newer kernel versions not common on older Android devices. Source [ highlighting ours -ed ]
1/20/2016 SCADA selfies
Would you take a picture of your network passwords and logic diagrams to post on line?
Supervisory Control and Data Acquisition (SCADA) has its origins in the 1950s and widespread in the 1960s. (see history). It is a system for equipment control using signals over multiple communication channels including the internet. As with many legacy systems they were not designed with security as a primary consideration and communications via the internet leads to exposures. So what security there is should be, well, secure, right? Ah, not so much.
We could write about traffic lights or pumps, but for a little more excitement let us watch the Battle of Veridian III from the Star Trek movie Generations. The Enterprise shields are operating at a modulation of 257.4 megahertz. Rather critical information as anything else modulating at the same frequency just passes right through. So what happens? Look at 1:12 in this 4:13 clip. The information is clearly displayed for anyone to see and abuse.
Any non-fictional examples? Sadly, there are. Some “selfies” show people and their background where network designs and passwords are clearly legible. So, if you are in a facility with some secrets think about what is a) posted on the wall or other background and b) who is taking pictures destined for public viewing. Also give a little thought to c) posting a no pictures placard. How many were affected by this kind of security slip up? No one knows! More at NakedSecurity/Sophos
[ As for how the Battle of Veridian III should have gone see this 1:34 clip -ed ]
2/03/2016 Update SCADA selfies
More examples, including guidance for Stuxnet, from PandaSecurity
1/20/2016 Stolen Apple Cookies
Cookies are client-side files, generally small and used for many purposes. The Captive Portal bug allowed hackers to impersonate end users that had connected to websites that use unencrypted authentication cookies. This was discovered by Skycure and reported to Apple in June 2013. The release of iOS 9.2.1 fixes the problem almost 30 months after it was discovered. More at ArsTechnica. How many were affected over 30 months?
1/21/2016 Australia’s Royal Melbourne Hospital, infected
The Royal Melbourne Hospital reported the hospital network had been infected with a virus causing disruption, inconvenience and potential exposure of patient data. The network runs on the discontinued Windows/XP and affects laboratory results, email and many functions. Hospitals are not generally considered traditional targets for financial gain, but they are a treasure trove of information valuable for identity theft. How many were affected? More at Phys.Org
1/25/2016 Skype – IP snatcher?
Not being a crook, and not playing one on even basic cable, I didn’t know that Skype allowed crooks to determine your IP address. The “Skype resolver” allows you to search Skype for someone’s account then determine the IP. Resolvers work regardless of user privacy settings.
Remember Skype’s privacy policy: “Skype is committed to respecting your privacy and the confidentiality of your personal data, traffic data and communications content.” On the other hand Microsoft has worked to handing over the keys to your privacy to allow the quiet tapping of video and audio portions of Skype communications. As of a few days ago an update will prevent these resolvers from working. On the other hand, Skype functionality is included in Windows 10 which expands the attack plane so does the update really matter? How many were affected by this insecurity? More at KrebsOnSecurity. [ Don’t know about anyone else, but that update causes my Skype to crash in 10 minutes whether I use it or not. I can’t leave it running. Geee, thanks! -ed ]
1/24/2016 E2E Encryption, except in the middle
Apple is a staunch proponent of strong encryption for the people, but …
For Apple’s iMessage service end-to-end encryption is supposed to mean only the sender and the receiver can read it. In a September 2014 interview (whole transcript) Apple CEO Tim Cook told Charlie Rose: “If the government laid a subpoena to get iMessages, we can’t provide it … It is encrypted, and we do not have a key.” That is except for the data stored by hundreds of millions users on Apple’s servers. After application of end-to-end encryption for these files stored in the iCloud Backup Apple keeps a key. (see iCloud section of Approach to Privacy) So copies of all your messages, personal (sometimes very personal) photographs and important data stored on your device are locked up except to you, or Apple, or anyone who hacks iCloud Backup. There is another way to back up your material. For that, How to Turn it off iCloud Backup and more see TheHackerNews.
[ How many were affected? As of 2014 there were an estimated half a billion users of iCloud, but the number using it for backup were unknown. Again, no one knows, but more than a few celebrities whose very personal photographs were hacked and displayed, the answer might be too many. -ed ]
1/26/2016 Israel Utility Attacked
Israel’s Electric Authority is experiencing a “severe cyber-attack”.
According to the TimesOfIsrael Energy Minister Yuval Steinitz said steps are being taken to counter the assault. Number of affected persons is not known. More at DataBreachToday
1/28/2016 Update: Israel Utility Regulatory Body Attacked
Sometimes the loudest voices speak not-quite-the truth, let alone the whole truth. That misinformation may be deliberate or simply not knowing. Given the prevalence of sound-bites and internet speed that misinformation echoes around the world several times before the truth can take a single lap.
The Israel Electricity Authority (IEA) is a regulatory entity with fewer than 50 employees one of whom fell victim to an email phishing attack. The opened email attachment loaded ransomware. The IEA disconnected their systems to contain the ransomware from spreading. More …
1/26/2016 Lenovo Hard Codes Password & more
The 3rd worst password of 2015 allows open, unencrypted networks.
One of the world’s largest computer manufacturers, Lenovo, hard-coded a password in the file sharing software SHAREit. This time the flaws allowed the creation of a WiFi hotspot without any password allowing a crook to capture data between Windows and Android devices. Encryption? Nah, they didn’t implement that either. Security researchers reported the problems to Lenovo in October 2015 and the patches are just now becoming available.
This isn’t Lenovo’s first time providing large scale not-security. Laptops were shipped with SuperFish adware, they’ve installed unremovable software and spyware. How many were affected this time? No one knows. More at TheHackerNews.
1/26/2016 Magneto e-commerce exposed
E-Bay’s Magneto has a major weakness.
The weakness allows crooks to take over a Magento-based online store, escalate user privileges, and swipe customer data including charge card information. How hard is it to infect a site? Embed JavaScript code in a field for email address. Magneto takes care of the rest. How many were exposed? Magneto runs on over 10 million of web sites, but the number of sites affected and the number of consumers compromised is unknown. For patch information and more see TheHackerNews.
1/26/2016 Major Spyware found in Australian date center
According to researchers, spyware installed in Australia was placed there by Indonesia.
The actual beneficiary of the spyware is hidden with a proxy server inside the data center. Identified as “FinFisher”, developed by Gamma Group of Munich, Germany, it is sold only to government agencies in support of law enforcement. The powers of the software have been abused in the past. How many were compromised by this spyware? No one knows. More…
1/27/2016 TP-Link Routers
Manufacturers are somewhat conflicted about devices with user controlled security
If they ship with no security at all and user does not change it (many don’t) then there is no security. A one-for-all default security isn’t much better. One compromise is to create a special password for each. Some companies print that on a card, but then there is the problem of getting the cards with the devices.
TP-LINK went one better and put the password on the same sticker for their wireless router that shows the MAC address and default wireless name (SSID). The problem? That new password is actually the last eight characters of the MAC address. Why is that a problem? The Media Access Code, or Medium Access Code, is theoretically unique in the world and far from being secret, is included in every packet so as not interfere with other devices. So how many were exposed? No one knows. For guidance on what to do and more see this NakedSecurity/Sophos article.
Change those default settings!
Security is in YOUR hands!
1/27/2016 Wendy’s Breached?
A number of banking sources in the midwest sparked a query by KrebsOnSecurity.
Once again, a “first report” comes from an independent security researcher and not the company itself. More reports from the east coast found a pattern of compromised charge cards with antecedent uses in the Wendy’s chain of fast food restaurants. Details are scarce but if this is a systemic exposure it could be huge as Wendy’s includes about 6,500 restaurants in the United States, US territories and countries in Africa, Asia-Pacific, Caribbean, Europe, Latin America, Middle East, and North America. Wendy’s joins Dairy Queen (see 8/27/2014) and Jimmy John’s. For more see KrebsOnSecurity
3/02/2016 Update Wendy’s Breach
Wendy’s confirms malware found. Credit unions reporting high fraud.
In the 2015 annual report (preliminary version) the company reported that it does not yet know how many stores or customers were affected. Some credit unions are reporting high levels of debit card fraud that struck in January before the story went public. One reported that before the end of January 2016 the fraud cost was half of all of 2015. More at Krebs on Security
5/12/2016 Update Wendy’s Breach, 6 months later
Perhaps six months after malware started to swipe consumer charge cards, Wendy’s has reported malware infected point-of-sale (POS) terminals at “fewer than 300” of approximately 5,500 restaurants in North America and started in the fall of 2015. This disclosure was between “Company on track to achieve 2020 North America system goals” and “Same-restaurant sales reporting methodology”, about the middle of 2016 First Quarter Results. More at Naked Security / Sophos
[ So they either don’t know, or won’t reveal, the exact number of infections. If the former, how to they know it isn’t more than 300? There is a FAQ that is similarly short on details. The news is rather buried. -ed ]
5/13/2016 Update Wendy’s Breach, Class Action
In late-April a class action complaint was filed by multiple credit unions saying Wendy’s “pervasive and inadequate approach to data security” caused unspecified damages. The lawsuit stated: “Taking advantage of Wendy’s lax data security and delayed notification to financial institutions and the public, hackers were able to gather large amounts of consumer data …”. “Unknown perpetrators also specifically targeted and drained debit accounts with large amounts of money in them, concentrating the damages and causing individual financial institutions … to suffer losses much greater than what was experienced after the Home Depot or Target data breaches.” More at CNBC.
[ Recall that credit unions were slammed hardest and earliest in January 2016 and that was many weeks after the breach in late 2015. Bolding in the quoted text is ours. -ed ]
6/09/2016 Update Wendy’s Breach – Larger than reported
In late January 2016 Krebs on Security broke the story on multiple charge card fraud with Wendy’s being a common point for many. Eventually Wendy’s admitted the breach reporting about 300 stores were affected. A class action suit was filed by credit unions who were damaged by the reporting delay. Today the company acknowledged the breach is now expected to be “considerably higher than the 300 restaurants already implicated.” More at Krebs on Security
7/07/2016 Update Wendy’s Reporting: A pattern
A quick recap of events.
March 2016 – Wendy’s confirms a breach.
May 2016 – Wendy’s reports “fewer than 300” restaurants affected.
May 2016 – Class Action lawsuit filed.
June 2016 – KrebsOnSecurity reports breach numbers are going to be larger.
July 7, 2016 – About 1,025 restaurants affected, 4x more than Wendy’s report.
The number of customers affected still unknown or undisclosed. The information appears to be “out there” and Wendy’s is the last to report it.
1/28/2016 LG G3 phones
All are vulnerable thanks to a pre-installed “feature” discovered by Israeli researchers.
While there is a G4 moving into popular use, the G3 is LG’s most popular model. It has an application called Smart Notice which displays notifications. The problem is the notifications can be made to inject program code which can control the device, steal data (including very personal pictures and charge card information) and more. The compromise works in two steps. First part grabs the telephone number and ID from the phone’s memory. Then it accesses a web site to download the malware. LG has released a patch and it is highly recommended.
See Times of Israel and for more details on the exploit see ArsTechnica. How many were affected? No one knows.
1/29/2016 India Banks hit by ransomware
Earlier in January 2016 ransomware affected computers at three banks and a pharmaceutical company. The ransom demanded was one bitcoin each for each computer, millions of dollars. Companies in India tend to be secretive about such attacks, not only to save “face”, but because the transfer of bitcoins is not yet legal in India. In June 2013, the Reserve Bank of India (RBI) wrote that virtual currencies posed legal, regulatory and operational challenges. In December 2014, RBI advised the Indian public to be cautious in buying and selling of virtual currencies. As a result, paying a ransom in bitcoin is an offense that could result in prosecution. More at DataBreachToday. Related: Read what Rudyard Kipling wrote about such payments.
January 2016
In addition to others shown here in January 2016, ITRC reported 11 incidents where the number affected was unknown or undisclosed.
2/02/2016 Two more IOT leaks
The Fisher-Price smart toy bear leaks customer and kid data. Again, this was discovered by an independent security researcher and not the company. The bear’s backend (no pun intended) collected the names of children, birthday, gender and other profile information. That software was not secured. Mattel addressed the issues about six weeks later, but why, in early 2016, were such vulnerabilities even present in a device such as this? The same researcher found the “hereO” GPS watch designed to track wearers while allowing message transfers. It is similarly leaky allowing unintended parties to track wearers and their location. Again, the bugs were fixed and again, how were they allowed to get to a device in the hands of a consumer? More in this article from Fortune.
2/04/2016 WordPress sites targeted
(just what we don’t need)
ArsTechnica published a story about 2pm Central today. Miscreants are hacking web sites created with the popular WordPress content management system (CMS) so that visitors (users) get some extra malicious code. That malware redirects the visitor to other sites where ransomware is delivered. Visitors are known to be vulnerable if they use out-of-date versions of Adobe (Flash Player or Acrobat Reader) or Microsoft (Silverlight or Internet Explorer). The malware command and control domains are being blacklisted (so users can’t get there), but new ones are being created. According to the article this exploit code was detected by just two of 66 antivirus packages which reflects the first-mover advantage of crooks and the limitations of reactive response vs proactive prevention.
If you are a web site developer using WordPress forward this post or the Ars article to your hosting company and ask if they are aware of this. Do that now. Then check your site with this from Securi https://sitecheck.sucuri.net//
[ Remember to backup your critical information on media not connected to the machine. This air-gap means the virus can’t reach them to contaminate them. Not all ransomware follows through on unlocking even after you pay. Further, is your machine really clean of the virus or have they made a note to revisit you later? Read what Rudyard Kipling, Nobel Laureate in Literature in 1907, wrote circa 1911 about paying tribute See also this guide from Comparitech on how to prevent & remove ransomware -ed ]
2/05/2016 Now Netgear
Netgear routers found vulnerable to two ways to compromise your network and devices.
The critical vulnerabilities are in the web interface for Netgear’s ProSafe NMS300 Model (Network Management System) that uses Simple Network Management Protocol (SNMP) to gather data from networked devices. The vulnerabilities are Upload and Execute any malicious file remotely (CVE-2016-1524) and Download any file from Server (CVE-2016-1525) (see SecLists.Org for details on both CVEs) More details at The Hacker News.
2/07/2016 iPhone Lock Screen? What Lock Screen?
The passcode lock screen on iOS8 and iOS9 can be bypassed.
“An application update loop that results in a pass code bypass vulnerability has been discovered in the official Apple iOS (iPhone5&6|iPad2) v8.x, v9.0, v9.1 & v9.2. The security vulnerability allows local attackers to bypass pass code lock protection of the apple iPhone via an application update loop issue. The issue affects the device security when processing to request a local update by an installed mobile ios web-application.” Video 6m 10s More at Security Affairs
2/08/2016 Nothing spreads a virus like a Trane!
The Trane internet-connected thermostat has a bug. Hardly news, far too many things on the internet have bugs, but this is a story reflecting a lack of planning and response deficit which puts the Inherent Danger in the Internet Of Things.
Cisco security notified Trane that its “ComfortLink II” thermostat had a number of security flaws including hardcoding of passwords and a buffer overflow vulnerability could allow remote code execution. Both make a public-facing device easier to compromise. The warning was sent in April 2014, and June, and August and September. No response from Trane. April 2015 Trane fixed the hard coded password problem in a release of firmware. Trane fixed the other problems in January 2016, but never told its customers. Some devices do updates automatically, not the Trane. The updates are manual and require downloading to a memory card and more.
Therein lies the design problem. Companies are focused on getting product out the door, you know, sales. Few consider the product they are shipping is already defective and will need updates. Some need frequent updates. If those are not automatic then the installed base of vulnerability grows and we get exposures on the Heartbleed scale. More at TheRegister/UK and related from KrebsOnSecurity
2/08/2016 ATM cards without limits? Not really.
As we’ve written before crooks ain’t dummies. If it were not for the criminal part of their activities some of the work they’ve done is downright admirable.
One of the detection methods used to spot ATM abuse is excessive activity measured by transaction frequency or value. What if those parameters were reset after each transaction? Welcome to the “Metel crimeware package”. Over 30 modules are tailored to the targeted computer. The “rollback” capability allows nearly unlimited sums to be withdrawn from ATMs belonging to a bank other than the one that provided the card. Not theory, the rollbacks already cost some banks dearly. More at ArsTechnica
2/08/2016 TMZ bit by Angler
Who knew that malvertising could pay off so handsomely?
The celebrity gossip site TMZ has joined Rotten Tomatoes, Jerusalem Post, LifeBuzz, and more as victims of malvertizing. The concept is straightforward and increasingly profitable. A crook buys ad impressions from a reputable company for as little as $0.14 per thousand impressions (CPM). Some user lands on the ad page, vulnerability checks are made and malware is delivered. Eventually enough feedback is provided to the company that they halt the advertising campaign, but it is whack-a-mole. Crooks create new profiles and start all over again. They can use anonymous proxies and the CloudFlare infrastructure to hide their servers while encrypting their traffic. More from Graham Clueley
[ Herein lies a problem for business and the public. Some sites such as CBSNEWS.com are requiring adblocker disabling before displaying content, but is CBS responsible for damage to me from malware hiding in ads they serve? Don’t think so, so sorry CBS. It also raises a problem for those web sites depending on ad revenue. Where is the balance when consumers are compelled to drink from a poison-laced well? (from 2/5/16) -ed ]
2/08/2016 Are you taking a survey or … ?
Would you take a brief survey for £10? Are you actually taking a survey or are you participating in a phishing scam? Amazon’s identity has been used to extract financial information from unwitting participants. See MalwareByes.Org from 2/4/2016 and more at International Business Times / UK from 2/5/2016.
2/08/2016 T9000 cyber espionage tool
The T9000 targets specific applications including Skype users.
It identifies potential security products (listed in Palo Alto URL below) arrayed against infection and utilizes specifically created evasion methods. It even breaks installation into multiple stages to thwart (or at least delay) security analysis. The goal is data capture and copy files of specific types. Great detail at Palo Alto Networks (from 2/4/2016) and a good summary at Net Security (from 2/8/2016)
2/09/2016 Running Fred
If there was an app from hell it might have been this one.
In the beginning there was “Running Fred”, a pleasant game that ran in Google’s Chrome browser on a desktop or mobile device. Unscrupulous developers removed the highly rated game that had 200,000 users and turned it into something akin to the Running Dead, zombies that will never, ever stop terrorizing your life, won’t ever truly die and operate faster than we can. The new app would open new windows or tabs, reset your home page, load other games, seek BUY buttons and incur purchases without the user ever seeing, let alone approving, the purchase. The Federal Trade Commission (FTC) filed a complaint (6 page PDF) with the company General Workings Inc. (GWI) which did business as Vulcun and the two developers who were also GWI officers alleging “unfair practices” including bypassing the permissions process allowing unauthorized access to other data (address books, images, location etc) in the device. There was a settlement (8 page PDF) where the developers have to ‘fess up and follow the rules established for disclosure of permissions requested and obtain affirmative consent to use those permissions. Fines don’t appear to come into play unless the developers violate the settlement. How many were affected by this dread-ware? No one knows. More at Naked Security / Sophos
[ which brings up the question: Just how easy is it for an app to bypass permissions in the first place? -ed ]
2/11/2016 Apple Sparkle Vulnerability
Sparkle facilitates background automatic updates in OS X. Many third parties use it and expose you to a vulnerability. Some app developers use an unencrypted HTTP URL to check for the existence of a new updates. Crooks could fake that, perform a man-in-the-middle attack to inject code and obtain control. Over 700 apps are known to use Sparkle. How many are vulnerable? How many have been exploited? How many users affected? No one knows. More, including a proof-of-concept video at The Hacker News.
2/13/2016 IRS & U
Multiple stories related to the Internal Revenue Service.
Attacks from Without
Back in May 2015, the IRS detected that a third (not you and not them) party had accessed about 100,000 accounts via the GetTranscript application. It was later determined it wasn’t a “hack”, but weak authentication used in the protection of taxpayer data and the exposure was over 330,000.
A few days ago the IRS issued a statement which says “… we identified unauthorized attempts involving approximately 464,000 unique SSNs, of which 101,000 SSNs were used to successfully access an E-file PIN.” which means they had all those Social Security numbers already and used them to breach the requirement for a personal identification number (PIN) to efile. So two factor authentication (2FA) in the form of SSN and PIN has already been materially compromised. Now the IRS had reported it “stopped” a hack, but in the next breath we hear about all of this. Which is it?
Attacks from Within
Just yesterday, an Alabama-based IRS employee admitted stealing taxpayer identities to claim $1.5 million in fraudulent tax refunds of which over $400,000 had already been collected. The zinger? That employee’s job was in Taxpayer Advocate Service, helping victims of identity theft victims on correcting their tax information. Which brings to mind:
Who will guard the guards themselves?
In addition to giving back funds received there could be fines over a million dollars and up to 30 years in prison. There were other accused accomplices. More at Fortune.
How many were affected? From the most recent attack two are known. How many others?
2/13/2016 Cool Kohl’s Cash
Combination hack and theft with a twist.
Shop at Kohl’s, spend $50, get $10 in “Kohl Cash” usable for further purchases. Crooks hacked an account, changed the email address, and ordered large items. Why? Because Kohl credits the consumer’s Kohl Cash account at purchase and reduces when items are returned. Large items are harder to return and by then the crooks have redeemed the Kohl Cash for items to re-sell or near-cash-equivalents such as gift cards. The email address gets changed so the crooks know when the purchase has been made, but the consumer does not. Changing the delivery address might raise flags so they don’t. How many were affected? No one is saying. According to one source this isn’t a small target. In 2011 about 2.6 billion loyalty memberships generated $48 billion in rewards. More at KrebsOnSecurity.
[ Just the type of crime NC3 was designed to combat without imposing heavy requirements on the merchant. The authorization could have been recurring with a not-to-exceed amount and notification outside of Kohl’s control when the charge was made. -ed ]
2/14/2016 Mazar BOT
One word summary: OUCH!
It starts with a text message something like this
You have received a multimedia message from +[country code] [sender number] Follow the link http: //www.mmsforyou [.] Net / mms.apk to view the message.
APK is an Android program file. If tapped or clicked it will gain administrator rights on the device allowing attackers to:
Read the phone’s state and change it
Change the phone settings
Create, Send, Receive and Read your SMS messages
Initiate calls to your contacts
Access the internet
Completely wipe the phone’s storage
Inject malware into the phone’s Chrome browser
The malware can download the TOR browser and the Polipo Proxy. This allows the malware to send messages, browse the internet and execute masked attacks on others.
Current antivirus detection of this APK is under 6%, just 3 of 54 AV packages detected Mazar BOT. How to stop it There is a key step under complete user control. Do NOT tap or click on an incoming message that contains a link to install ANYTHING. Also – go to Settings | Security, find the option that says “Unknown Sources – Allow installation of apps” or “Allow sources other than the playstore to install apps” and make sure that is UNchecked.
More at Heimdal Security. In October 2015 Britain’s GCHQ was reported to have a more powerful capability where a specially-crafted text message is never even seen by the user. Once infected the phone can now have its microphone activated, take pictures, see storage on the device and report its location with greater accuracy that generally available GPS. How many have been affected by Mazar BOT, GHCQ or NSA malicious messages? No one knows.
2/19/2016 Support Opens Doors for Hackers
Support bundle includes remote control software with no, or a predictable, password.
Comodo Antivirus, Comodo Firewall, and Comodo Internet Security all bundled an excellent remote control server software. Unfortunately that software wasn’t set with good password protection. Knowing just the IP address and a port number was enough. Subsequent version were the first eight characters of a known signature algorithm applied to several known attributes. The damage may have been limited, but how many were affected? No one knows. More…
2/21/2016 Price for being a leader
Linux Mint, a leading distribution of Linux, was hacked. The ISO images for one version was replaced with another image that included a back door. The malware laden images would not pass the checksum provided. The company has been very open in describing what happened, what they have done, how to spot the malware laden versions, and what to do if you found it. The community has responded with some additional concerns and the company is addressing them rapidly. See the reporting blog at http://blog.linuxmint.com/?p=2994
2/22/2016 Update Linux Mint
How it was hacked, forum breach, beware spear-phishing attempts.
Popularity Earlier we reported that Linux Mint was “a” leader of Linux distributions. We were wrong. Linux Mint is “the” leader. According to DistroWatch over the last 12 months, as rated by hits per day, Mint is first at over 3,000. Followed by Debian (1900), Ubuntu (1600), openSUSE (1350), and Fedora (1100). The numbers change with each update to the database, but the top 3 spots are Mint, Debian and Ubuntu, in that order, for all time frames 6 months, 3 months and 1 month. The popularity of Linux Mint is not the core-Linux functionality. Mint is based on Ubuntu which is derived from Debian. The big difference is the user interfaces. Mint provides several and many new users appreciate the less-intimidating Mint.
So what happened? The hackers were able to replace a PHP script that directed users to a fake download page which directed them to download the malware laden ISO image from a look-alike, sometimes called impostor, web site.
Good news For each version Mint is packaged in six varieties based on desktop design (Cinnamon, KDE, or Xfce) each of them in 32-bit or 64-bit code appropriate for your computer. Only Cinnamon-64 for version 17.3, was compromised. Hacker’s didn’t affect source code, or the actual ISOs, or the validations checksums. Anyone who installed that version and did not check the checksum should evaluate their installation (see link above) and their installation disks.
Bad news On another blog post http://blog.linuxmint.com/?p=3001 Clement Lefebvre (Clem, founder and Mint project leader) reported the forum database was taken exposing username, password (encrypted), your email email address, personal profile information and what you posted including private topics or messages. In short beware of spear-phishing that may appear to come from Mint.
February 2016
In addition to others shown here in February 2016, ITRC reported 30 incidents where the number affected was unknown or undisclosed.
3/07/2016 Mac Targeted with Ransomware
A pain for Windows users has been shared with the Apple Mac community
KeRanger ransomware is targeted at Mac OS X users. It appeared in early March disguised as an RTF document inside an installer of a legitimate application. The malware was signed with a legitimate Apple developer certificate and would slip right past Gatekeeper protections. According to scanning service VirusTotal, as of early March 7, only 2 out of 54 anti-virus scanners detected KeRanger. For how it works, how it propagates and how to protect yourself see The Hacker News.
3/08/2016 Another W2 phishing success, for the crooks
Environmental Resources Management (ERM) issued a letter (source: KOS) disclosing that on 2/29/2016 an email, reportedly from “senior management”, was successful in obtaining personal information for current and former employees via W2s for their former “Northern Division” which included multiple companies. The number effected was not available.
3/11/2016 Irony Strikes “High Security” web Hosting Company
Staminus, which portrays itself as high security, was hit with DDoS attack and hacked.
Staminus Communications Inc. is an internet hosting company that specializes in protecting its customers from being knocked off line by distributed denial of service attacks. They themselves were taken off line for about a day. During that attack it appears that someone hacked the company and posted public links to what appears to be customer user names, passwords, support tickets, charge card numbers and more.
Adding insult to injury the hackers posted (picture) what not to do if you are a security oriented web hosting provider. One of those insults was keeping charge card information in plain text, a violation of PCI-DSS rules. Confirmation of charge card exposure and number exposed are still pending.
The company “went quiet” even though their FaceBook and Twitter feeds were overflowing with comments from customers growing more irate by the hour. Reporting something is better than silence. More at Ars Techica and Krebs On Security.
3/13/2016 Oracle: Java fixed … maybe not
October 2013 Oracle released a patch to CVE-2013-5838 and reported all fixed. Apparently not and millions of Java users are still vulnerable 30 months later. The report (6 page PDF 3 pages are title, disclaimer, and footer) created by Security Explorations researchers describes proof-of-concept code and report it was successful in breaching a Java security sandbox. More at Ars Technica
3/28/2016 More POS Malware
FireEye has spotted new versions of TreasureHunt a point-of-sale malware targeted at non-EMV systems. More at FireEye
3/29/2016 Another hospital time warps to 1970
MedStar, with 10 hospitals, 250 outpatient centers, 30,000 staff, and 3,000 doctors in Maryland, Virginia and DC reverted to all-manual methods due to cyber attack which denied access to records, emails, directory and more. Systems were disconnected to contain the infection. As of mid 3/29 there was no report of ransomware or the purpose behind the attack.
[ Hospitals are susceptible to attacks on its equipment, they tend to focus on protecting data (not patients) and are having a hard time training people and otherwise protecting themselves from ransomware. -ed ]
3/29/2016 Update Medstar got ransomware?
Late Tuesday evening: Although officials would not confirm, a number of employees have reported seeing a popup demanding a ransom of 45 bitcoins (about $19,000) in 10 days. Manual charting was reported as chaotic as less experienced personnel had never done manual record keeping. Some medication with potentially life threatening complications could not be used because the patient records could not rule out the possibility of the complication. By the end of the day emergency patients with time critical treatment requirements were being accepted. The other, non-critical, patients were diverted to other facilities. Patients who depend on time-critical follow up care, such as cancer patients, are having appointments canceled. Extended delay could have negative consequences. (Source)
March 2016
In addition to others shown here in March 2016, ITRC reported 59 incidents where the number affected was unknown or undisclosed.
4/04/2016 Trump Hotels, breached … again.
After being contacted by security researcher Brian Krebs, Trump Hotels has acknowledged that it is investigating after three sources noticed a pattern of fraud on customer cards who had stayed at the hotels. An earlier breach was announced by the same researcher in July 2015 which may have started in February 2015 or earlier. It wasn’t until September 2015 that the company confirmed the breach had started in May 2014 and ran for more than a year without detection. More at Krebs On Security
4/04/2016 Panama Papers
Information kept from the public occasionally comes to the light and the exposure demonstrates why the phrase “Secrecy Begets Tyranny” rings so true.
United States – Vietnam Relations, 1945-1967 was prepared by the Department of Defense and described the purpose of the war, attacks in neighboring countries, how the US had created “South Vietnam”, supported Diem, then supported a coup against him. These were the Pentagon Papers, about 3,000 pages of history and 4,000 pages of analysis guarded at the highest level and kept secret kept from the people, the Congress even the National Security Adviser. It contradicted many public statements marking those statements as lies. The study was prepared by military and civilians including Daniel Ellsberg who later copied the 7,000 pages. In the early 1970s some pages were leaked to the New York Times, but over 4,000 pages were read into the Congressional Record which makes them very hard to disappear. 7,000 pages might be 50 megabytes today, depending on the graphics.
In November 2010 WikiLeaks published the first of many classified State Department communications from December 1966 to February 2010 containing opinions and analysis on countries and their officials. In total there were over 250,000 cables perhaps 2 gigabytes.
The first exposed lies told by the US government about a long and unpopular conflict. The second exposed a considerable amount of domestic and international surveillance activities.
The records of a single law firm in Panama have been exposed in over two terabytes. The number of documents are staggering: Over 4 million emails, 3 million database elements, and 2 million portable document files, representing decades of work.
What were in these Panama Papers? They appear to describe hundreds of shell companies used to hide client assets. The denunciations are coming from the company and some of the individuals named. Some countries have announced investigations for potential charges of tax evasion by the President and former President of Azerbaijan, the current President and a Former Prime Minister of Ukraine, Ministers, political party officials, a professional soccer player, and more.
On thing is for certain: The law firm wasn’t paying attention to our story and updates in early 2015 and this update from March 2016 or they might have taken better protections. The fallout will happen over years.
More at Organized Crime and Corruption Reporting Project (OCCRP), Wired and AOL (excellent video summary)
[ The total size of the files may partly be due to the bloat that has crept into even routine word processing. In the old days a single character could be presented in a text file as one byte. Save a single character in a modern word processing document and that file might be 9,000 bytes. – old ed ]
4/05/2016 Update Panama Papers
“Panama Papers” is a nice alliteration as opposed to the “Panama Electrons” which sounds like a local gaming group.
Why not paper? Naked Security / Sophos did an analysis and found that printing the estimated 2.6 million pages would have resulted in a paper pile weighing 13 metric tonnes, about 14.3 tons, or about 28,600 pounds. That is using A4 paper at 5 grams a sheet. Rather hard to smuggle out in a briefcase.
Follow the script. NOT THAT ONE! They also found the law firm’s representatives were following the script book almost letter perfect for What you sound like after a data breach. What the representative may not have realized is that particular article was sarcasm.
What was it? It appears that the first step toward unauthorized access was a compromise of the email server. More at the source.
4/05/2016 Update Panama Papers – First Blood
After insisting he would stay in office, Sigmundur David Gunnlaugsson, the Prime Minister of Iceland has resigned.
Why? In 2007 the Panamanian law firm created a company for him and his partner in the British Virgin Islands. The partner became his wife. The company lost millions of dollars in the 2008 in Iceland’s banking crisis. On the last day of 2009, just before a new disclosure law went into affect, he sold all his company shares to his wife for one dollar. In 2013 Mr. Gunnlaugsson became prime minister. As such he was involved in reaching an agreement on such claims. He did not disclose any conflict of interest. More at NYTimes
4/06/2016 Update Panama Papers – Interview before the bomb
In an interview, the week before the disclosure, the two partners in the law firm were already retreating from their long practiced growth intentions and scaling back. One partner was frustrated by the political ambitions of the other as those ambitions were drawing what neither wanted, public attention and regulatory scrutiny. Those shell corporations were created in the British Virgin Islands (about 113,000), Panama (±48,000), Bahamas (±17,000), Seychelles (±16,000), and more. The State of Nevada was the 8th most popular with about 1,000. (Bloomberg Article also has video 3:54)
4/07/2016 Update Why hack law firms?
Are law firms exempt from hacking? Are hacks of law firms under-reported? So, why hack a law firm?
6/06/2016 Update Panama Papers / How it worked
When First We Practice To Deceive”
So how did a firm in Panama make it possible to avoid, or evade, US tax law? The NY Times uses several, very specific examples, on how tens of millions of dollars was shuffled around, reported (or not) all to the benefit of those who can pay for it and make the moral decision not to pay taxes due. It is not a simple read as the deceptive practice created a tangled web indeed.
4/06/2016 What is old is new again
There is no denying that malware has gotten more sophisticated. Meet “Petya”, retro malware.
Late 1980s saw some of the earliest forms of malware in the form of destructive viruses. There was no attempt at profit-taking, just screwing up hard drives. One technique worked faster than average and that was to leave the contents of the drive alone, just randomize the index to the contents. Once this directory was compromised, even though the parts were around, they could not be re-assembled easily. Petya is lean and mean. It pops up a fake message so consumers won’t yank the power cord while it is working. It runs from the master boot record (MBR) before most security services are even loaded.
The good news? MBR technology for booting has generally been replaced with something else. The bad news, MBR itself is kept for backward compatibility and Petya overwrites the new technology without backing it up first. So, even if you pay you won’t get unscrambled.
Your power? Don’t let it run and backup, Backup, BACKUP! Having to reinstall the operating system and files are better than losing them forever. See Naked Security / Sophos
4/12/2016 Update Petya Removal
Infected by Petya? Have hope. A well-motivated security researcher (father-in-law’s computer was infected by Petya) found a weakness. Putting that solution to use was a bit beyond the average computer user. Another researcher made it easier. See the step-by-step instructions via The Hacker News
4/06/2016 Apple Lockscreen Bypass
Got an iPhone 6S or 6S+ running iOS 9.2 to 9.3.1? Your lock screen is busted.
Thanks to Siri and some clever twists anyone who has physical access to your device can bypass the lockscreen. The good news is that you can disable Siri and block this exploit. See The Hacker News.
4/06/2016 Microsoft Authentication Bug
Microsoft’s main authentication system for Outlook, Azure and Office accounts is vulnerable. No one knows how many were affected. Microsoft paid a bounty to the discoverer and patched the vulnerability within two days. More at The Hacker News
4/07/2016 Chrome Extension Hijacked
A developer sold his well-received extension to the Chrome web browser a few months ago. Unfortunately the new owners added some code redirected web traffic through a proxy service before taking them to the web site they wanted. Along the way about half the users got a page with advertising. In addition to generating ad revenue the web traffic patterns of those users were collected and the resulting analysis also sold to advertisers. More than one Chrome extension has been hijacked with much the same code. For the list see Naked Security / Sophos.
4/07/2016 Commonwealth Edison, Illinois
Commonealth Edison, ComEd, is an energy delivery company serving about 3.8 million customers, about 70% of all residents in northern Illinois.
Like many utilities ComEd is trying to cut costs while improving service. One way is with electronic billing. It saves trees (no paper), reduces pollution (no mail trucks required), saves time (get there quickly) and has other benefits. Unfortunately they missed a point. Delivering plain-text personally identifiable information (PII) also cuts security. Here is a recent bill.
The fuzzy areas showed name, address, and account number. You can see class of service, type of service, actual usage, the amount due on the current bill, any past due amounts, and the date the meter was read. This information supports a social engineering scenario for a non-ComEd person to access the property or someone to call ComEd and change, or terminate services. Would you post this information for all too see? Probably not, but ComEd sent this information via email without any protection. Given the technology available today each consumer could easily set their own password so the portable document files (PDFs) ComEd uses to send invoices could be password protected before a few million of them are used by crooks.
4/11/2016 Irony bites
You want some video security. You research the options and find a good device on Amazon. You buy it and get hacked. Why? Because that new-in-the-box video security camera had malware. Amazon didn’t discover it, an independent security researcher did. How many were infected? No one knows!
4/12/2016 Malvertising Strikes The Netherlands, HARD!
Almost 300 web sites have been infected with advertising that delivers malware (malvertising). That is a lot of ads. One infected site is Nu.nl, a Dutch-language news portal with over 50 million visitors in March alone. The malware includes some of the worst ransomware. How many were infected? No one knows. More at Naked Security / Sophos
[ In mid-March 2016 there was a massive malvertising attack affecting major web sites including the British Broadcasting Company (BBC), MSN and The New York Times.
Malvertising is a problem for business and the public. Some sites are requiring adblocker disabling before displaying content. Is that site responsible for damage to me from malware hiding in ads they serve? Don’t think so. So, who is responsible? There are many places to point fingers, but web sites who want us to drop our adblockers are asking us to trust them and all the participants in the chain. That is akin to unprotected sex. I trust my partner, but do I trust every partner my partner trusted?
Forbes is one such site and soon after users lowered their shields (because Forbes has great content) those users were served malware.
It also raises a problem for those web sites depending on ad revenue. Where is the balance when consumers are compelled to drink from a poison-laced well? Considering the billions of ads being served a day, users need to maintain the best defenses they can. There may be a solution: Host the ads on the same servers that serve the content. Serve ads free of malware. It is more work for the content providers, but it shows concern for their visitors, you know, the revenue providers. Until then, I’m keeping my shields up and practicing safe hex. -ed ]
4/18/2016 New Banking Malware Hybrid
GozNym, the latest banking trojan, has arrived using combined techniques to swipe your money.
US (22) and Canadian (2) banks have given up millions of dollars to the trojan hybrid GozNym. The users of Nymaim integrated part of the Gozi ISFB source code and Security Intelligence (from IBM) bestowed the moniker GozNym which targets business banking (28% of reported incidents), credit unions (27%), e-commerce (22%), retail banking (17%) and others (6%)
Nymaim is a depositor of malware that uses multiple techniques to remain hidden and active. It was almost exclusively used as a depositor of ransomware until it started using Gozi ISFB, a dynamic link library (DLL) web injection tool to launch banking attacks. Much more at Security Intelligence.
4/20/2016 Coin Counting – Their Way
Years ago bank programmers used to calculate the interest expense on all their interest bearing accounts in total. Then they’d calculate the interest on each account and round fractions down. Fractions of a cent mean little, but the sum of all those fractions added up to another paycheck each week. Banks didn’t catch it because the total interest was correct.
Banks don’t pinch fractions of a cent much anymore, partly because most of those interest bearing accounts have stopped bearing interest. So, today they pinch whole pennies and more
The accuracy of coin counting machines have been questioned by many, but few go to the trouble of counting their coins in the first place. Earlier in April, WPVI in Philadelphia tested coin counters at 17 locations and found one, just one, was accurate. Some counts were off by almost $50.00. The bank removed those machines from service, but how long have they been shortchanging (literally) the customers and how many were affected? (Associated Press via CBSNews)
4/30/2016 Update Coin Counting – Their Way
The lack of quality control, maintenance, or whatever that prevented customers from getting an accurate count has come back to bit the bank it its own wallet.
In a complaint filed 4/27/2016 an operator of multiple of coin-operated washing and drying machines contends that the under-counting is systemic and constitutes wide-scale misconduct.
On April 6, 2016, NBC’s “Today” show reported that TD Bank’s Penny Arcades fail to accurately count the coins placed in them. The “Today” reporter tested TD Bank’s Penny Arcade machines by placing $300 worth of coins in Penny Arcades at five different, random TD Bank locations. Each of these tests resulted in the Penny Arcade counting less than $300, with one machine counting only a total of $256.90 for the $300 worth of coins. The loss of $43 represents a loss of almost 15% of the actual coin value placed in the machine. [ This was paragraph 2 of the complaint Highlighting ours – ed ]
The suit seeks class action status and trial by jury under several statutes including the bank being engaged in deceptive acts and practices by offering an accurate, coin-counting service, while not providing this service. More at MoneyWatch.com via CBSNews
[ So, who dunnit? Did the bank have it done as a matter of practice? Did some programmers do it? If the machines passed tests “3 times a day” were the machines programmed to recognize tests like VW diesel emissions? Did anyone seize a machine before it could be sanitized? Or was it just poorly maintained equipment that wasn’t subjected to genuine quality control? -ed ]
5/19/2016 Update Coin Counting – Their Way – No More!
TD Bank is permanently retiring coin counting machines nationwide including those which could not count accurately. More at CBS News.
4/30/2016 Toy with a side order of malware?
Maisto, a maker of miniature and radio-controlled toy vehicles, had their website hacked to push the Angler exploit on visitors. Angler leads to Bedep which leads to CryptXXX ransomware. How did his happen? Maisto is running a version of Joomla Content Management System lacking multiple security updates. More at MalwareBytes. There is a touch of good news. If you were unlucky enough to be infected by Trojan-Ransom.Win32.CryptXXX which is a member of the Rannoh family there is a RannohDecryptor available to no-charge thanks to Kaspersky. The same tool will cure Trojan-Ransom.Win32.Rannoh, Trojan-Ransom.Win32.AutoIt, Trojan-Ransom.Win32.Fury, Trojan-Ransom.Win32.Crybola, and Trojan-Ransom.Win32.Cryakl.
4/30/2016 Android Smishing
Malware is being distributed to Android users via infected subdomains of an authentic domain name. For example Malware.Google.com. It is unlikely Google created the subdomain “Malware”. Although this exploit is currently targeting Russian users the concept is expected to spread.
The technique, named smishing, is where a simple message is transmitted via the short messaging system (SMS). The victim sees a valid domain name and clicks the link leading to a web session on the compromised subdomain. Once infected the malware obtains administrator privileges. Then it deletes user access to the malware while running in the background communicating with a control server, delivering your information and getting new instructions. It also sends messages to your contact list to infect others and spread. More at Hack Read.
4/30/2016 Electric Utility gets Ransomware
Lansing Board of Water & Light (BWL) in Michigan had up to date anti-malware. Even that didn’t stop a new malware. An employee opened an infected email and ransomware invaded the system. In response BWL disconnected computers which also affected their telephone system. Source
April 2016
In addition to others shown here in April 2016, ITRC reported 79 incidents where the number affected was unknown or undisclosed.
5/01/2016 Office 365 massively vulnerable, but
Back in December 2015 two security researchers found a way to gain unrestricted access to almost any business account and from there access company Outlook, Skype for Business, OneNote and OneDrive storage. How they did it, how long the exposure existed, and Microsoft’s rapid, but very non-public response at International Business Times / UK
5/01/2016 Closing Cost Scam
Similar to the “email from the CEO” scam, the victims are moved into an emotional state to turn off their thinking brain and activate the emotional brain. In this case people who are closing on a house receive an “urgent” email to wire closing costs to this account or the deal won’t close! It is a scam. Someone hacked the email of the real estate agent or closing attorney or other participant. Don’t take precipitous actions based in incoming email, phone call etc. Details at Chron.
[ This almost happened to me. See Saved by a Nose and the updates that follow. -ed ]
5/01/2016 Waze Navigation vulnerable
Since 2014 Waze navigation makes 50 million users worldwide vulnerable to stalking. There is a quick work-around: select “invisible” mode. Another vulnerability allows providing ghost cars to create false traffic advisories. See Times of Israel.
5/01/2016 Facebook hacked in July 2015
Since July 2015 Facebook internal networks had been “completely owned” by a hacker. Who found out? Another hacker hunting bounty. Considering all that data wouldn’t you be concerned? Facebook’s response was something else completely. More at Engadget
5/09/2016 Update Panama Papers hits more
Analysis on terabytes of data raises questions about who has these accounts and why, especially considering their positions and power over literally billions of dollars of other people’s money.
Found in the Papers are multiple trustees of the $9.5 billion dollar endowment of Columbia University New York who have links to a corporation in the Cayman Islands. (graphic) The New York University School of Medicine is listed as a “master client” of multiple off-shore entities and the CEO of Pabst Brewing company makes an appearance. More at Business Insider.
[ Wonder if all that was required to be disclosed? -ed ]
5/19/2016 Noodles
Reports of card breaches at some of its 500+ restaurants in more than 30 states have spurred Noodles & Company to get some outside help to investigate. More at Krebs On Security
5/23/2016 Update Noodles
A week after being reported by Brian Krebs, the company has made a public semi-sort-of-announcement as reported in the Denver Post. The breach may have started in January of this year meaning some consumers have been exposed for months prior to notification.
6/30/2016 Update Noodles reveals
On 6/28/2016 Noodles announced the exposure of charge cards was from January 31, 2016 and June 2, 2016, but did not reveal the number of cards exposed. The announcement also said: “On June 2, 2016, Noodles & Company discovered suspicious activity on its computer systems that indicated a potential compromise of guests’ debit and credit card data for some debit and credit cards used at certain Noodles & Company locations.” [ rather odd as Brian Krebs noticed it on 5/19/2016 -ed ] The list (1 page PDF) of 25+ compromised stores, all in Maryland. More at CBS / Baltimore.
5/19/2016 RunKeeper
Runkeeper is a fitness app made by FitnessKeeper Inc. of Massachusetts. The Norwegian Consumer Council lodged a complaint in early May. Why? Notifications turn the app on (even if you are not exercising) and then sends data to its advertisers. That is a violation of the privacy agreement. More at Ars Technica.
5/28/2016 Zameen of Pakistan
A hacker defaced and exposed the database of most popular real estate web site of Pakistan. Exposed were usernames, email address, weakly (md5) encrypted passwords, personal phone numbers and other information on registered users. More at Hack Read.
May 2016
In addition to others shown here in May 2016, ITRC reported 66 incidents where the number affected was unknown or undisclosed.
6/03/2016 CiCi’s Pizza
Since April 2016 more than half a dozen banks have identified CiCi’s Pizza as a common place used by compromised cards in a pattern of fraud. So who do they call? Krebs On Security who found CiCi’s didn’t want to talk to him. Neither did their restaurant managers Champion Management. In the end he reached an outside public relations firm, SPM Communications. Then to CiCi’s point of sale provider, DataPoint. Why wasn’t that helpful? Read more at Krebs On Security.
[ We wonder if we’ll ever find out how many charge cards were compromised this way? One thing appears certain, while a single compromised charge card can wreak (hopefully short lived) havoc on a consumer, it does not appear moving companies to better protect our information. See this eWeek article. -ed ]
6/06/2016 Update CiCi’s Pizza / TeamViewer
TeamViewer is a popular desktop sharing / remote control application. The CiCi’s Pizza (maybe) breach (maybe) was accomplished using hacked credentials. Was TeamViewer hacked to obtain those credentials? TeamViewer says absolutely not and one thing is definitely not a “maybe”: If you use TeamViewer change your password. More at The Hacker News
6/07/2016 Update TeamViewer
TeamViewer does not believe it has been breached and the hacks of other sites are due to people re-using credentials on TeamViewer that were already exposed recently or many years ago. More on what TeamViewer is doing at Data Breach Today.
[ If we’re told you once we’ve told you 103 times – one credential for one account! Some companies are taking advantage the data at the Have I Been Pwned site to check customer information they have and forcing a reset just in case the customer used the same credentials. If you haven’t been to that site, go, now! (There are only 10 kinds of people in the world. Those that understand binary and those who don’t.) -ed ]
6/08/2016 Update CiCiPOS catches 1+million?
Analyzing a ‘botnet of more than 100 infected point-of-sale systems found some were running CICIPOS.EXE which may have been used to capture the more than 1.2 million charge card numbers recorded in the viewed botnet logs from April 2016 to date. This suggests logs were purged and the number affected is higher, much higher. About half were from CiCi’s, other were taken from movie houses, Malnati’s in Chicago, hotels and other restaurants. More at Krebs On Security
7/19/2016 Update CiCi’s Pizza acknowledges
More than six weeks after Krebs on Security broke the story, CiCi’s Pizza acknowledged that some restaurants were infected in 2015, most in March of 2016, and were eliminated by July 2016. The list details the 130+ affected stores in order by state. Apparently the crooks tricked employees into installing the malware. More at KOS.
6/08/2016 Education Hit with Ransomware
Ransomware locked down all student exam results just a day before announcement. They had a backup of sorts, hundreds of spreadsheets. Recompiling delayed the announcement a month. Another university was less prepared. The University of Calgary in Alberta had insufficient backup to recover systems files and restore email system after ransomware infection. That cost them a $CAD 20,000 ransom in Bitcoins. How many more were infected? See The Hacker News
6/18/2016 Acer Store
Acer, a consumer electronics manufacturer in Taiwan, has reported that its US online store Acer.com was breached potentially exposing every single customer, regardless of location, over the past 12 months. Exposed information includes name, address, charge card number, expiration date and security code used between May 12, 2015 and April 28, 2016. How many? They are not saying. In 2014 Acer shipped 24 million computes. More at International Business Times (IBT).
6/23/2016 Citrix GoToMyPC
The remote desktop access service was hacked this past weekend. A password reset has been imposed on all users. It appears the attack was not based on a breach at Citrix, but was using millions of passwords from other compromises. How many accounts at Citrix were actually affected is not known, or not being disclosed. More at Krebs On Security.
6/24/2016 Uber Ooops
A brute force attack revealed Uber promotion codes up to $25,000 for one or more free rides. Uber’s response: “out of scope” and they referred it to the fraud department. This is the experience of multiple researchers over several months. More at The Hacker News.
More than a dozen flaws Uber’s app and websites allow access driver and passenger information. Details on 8 were disclosed. 4 were considered too sensitive. The free ride (see above) was one. Others include a $100 ERH (emergency ride home) code that could be applied on top of other promotion codes. The driver’s Uber Unique Identifier (UUID) could be retrieved several ways. Knowing the UUID can lead to exposure of a list of trips, path taken, driver details, cost, and locations and ultimately driver impersonation. More at Security Affairs
[ So exploiting a problem is fraud, but repairing the problem is “out of scope”? How many times was these flaws exploited? How many drivers didn’t get paid? -ed ]
6/27/2016 IRS, again
Last week the Internal Revenue Service (IRS) announced the end of the “electronic filing PIN tool” (e-File PIN). Also called the Identity Protection (IP) PIN, it was issued to taxpayers who were already victims. It was terminated abruptly because of more “questionable activity”. The authentication questions were based in static information available to hackers. Example: What street did you live on in 1999? The number exposed this time was not released. Other IRS problems: February 2016 and May 2015 100,000+ exposed.
June 2016
In addition to others shown here in June 2016, ITRC reported 40 incidents where the number affected was unknown or undisclosed.
7/26/2016 Another open database
Earlier this month Chris Vickery uncovered another misconfigured CouchDB which didn’t require a username or a password. It is managed by Automation Integrated and was open for at least a week. A company vice president, speaking with Vickery, said “no one” in the office was aware of the problem.
So why is this database important? AI “manages” it, but the data includes Oklahoma’s state police, the Oklahoma Highway Patrol, a bank and more. When notified the OHP didn’t believe the Daily Dot reporter, was hostile and insisted the reporter did not know what he was talking about. Images in the database included considerable security information and images viewable at Vickery’s post at MacKeeper. How many people accessed this database before it was secured? No one knows. More at Daily Dot.
[ The good news: Within hours of emailing information to AI Vickerly was called by them, thanked for his timely communications and reported the database was no longer accessible. That kind of response, as opposed to blaming the messenger, is more of what we need. Someone want to nominate Chris Vickery for a medal? -ed ]
7/31/2016 Krebs on Line 1
July 22nd, 2016 Brian Krebs reached out to the San Francisco-based Kimpton Hotels about a pattern of card fraud that appeared to indicate a breach at over 20 of their 62 properties. They knew nothing about it. More at Krebs On Security.
[ July 26, 2016: Kimpton issued a release straight from the “How not to play it” handbook starting with “your security is important to us.” The number of properties affected, the manner of gaining access, and the number affected is either unknown or not disclosed. Next to “60 Minutes is in the lobby” the worst way to start your weekend is hear “Krebs is on line 1”. -ed ]
9/01/2016 Update: Krebs on Line 1
More than a month after Krebs on Security reported on the breach, Kimpton acknowledged it. The breach affected cards used at some restaurants and hotels from February 16, 2016 to July 7, 2016. Here is the list in alphabetical order (not even sorted by state). More at KOS.
July 2016
In addition to others shown here in July 2016, ITRC reported 18 incidents where the number affected was unknown or undisclosed.
8/04/2016 Massive Leak at Urology Practice
A 28 physician urology practice in central Ohio was hacked. Over 400,000 files were extracted and posted for all to see. Analysis found network architecture designs, data flow, login details to multiple servers, payment notices and a lot more without having to enter a single password. Patient data, payment methods and other personally identifiable information (PII) were also exposed. Update: a more detailed analysis also found email archives, risk assessments, security policies, and more than one hundred human resource related items including policies, procedures, CV/resumes, doctor audio records, salary, employment dates and more. Total number exposed still not known. See Hack Read
8/22/2016 20 Hotels
8/15 – for more than a year malware scraped card information from hotels from California to Vermont.
HEI Hotels & Resorts of Norwalk, Connecticut operates about 60 hotels and resorts under a variety of brands including Hyatt, Sheraton, Marriott, and Westin reported that card skimming malware was found at 20 properties. (list) The malware captured card information including name, account number, expiration date and verification code between March 2015 and June 2016. How many cards were exposed? Unknown or undisclosed. 8/12 Notice #1 Undated FAQ Notice #2 More at CBS/NewYork
8/22/2016 Eddie Bauer hacked
Eddie Bauer reported point-of-sale (POS) malware was found in its retail store systems (not the web site) that had been in place for as long as six months before the malware was detected.
The 8/18 press release isn’t clear, but appears to indicate that over 350 stores in US and Canada were affected. As recently as July 5, 2016 Bauer indicated it was unaware of any problems during communications with Krebs On Security. (link updated for 8/18/2016 events). How many cards were exposed? Unknown or undisclosed. More at Data Breach Today.
8/27/2016 Payroll processor breached
The accounting payroll processing company Sage has been breached. Their customers are spread over 23 countries and include 280 businesses in the United Kingdom. Founded in 1981 Sage has over 13,000 employees around the world. The total number of persons exposed is unknown or undisclosed. More at eHacking News.
8/27/2016 Microsoft master security key, exposed
Backdoors in programming are less-secure openings into systems for easier development. In a good security practice these openings are removed before that software is released to the general public. Unfortunately Microsoft kept a “universal” backdoor and leaked the “golden key” allowing any user to unlock any device that was protected by process known as “Secure Boot”. How many users were exposed to this threat? No one knows. More at Ars Technica
[ This is an example of why such backdoors are simply poor security practice. The FBI’s demand for Apple to put one in the iPhone could have exposed all iPhone users in the same manner. (a long story) -ed ]
August 2016
In addition to others shown here in August 2016, ITRC reported 52 incidents where the number affected was unknown or undisclosed.
9/16/2016 a 3 year breach
“Clueless” might be the most polite way to describe the IT staff and post-of-sale (POS) servicer at a Nashville, TN facility with over 230 rooms. Have there been enough well publicized breaches so that any reasonable operator would want to check their own systems? According to the notice from the Hutton Hotel, the POS systems were compromised and transmitted card holder name, account number, expiration date and verification code for front desk charges between 9/19/2012 and 4/16/2015. Between 11/15/2015 and 6/10/2016 charges made at dining facilities were also compromised. The number of compromised accounts is either unknown or undisclosed.
September 2016
In addition to others shown here in September 2016, ITRC reported 40 incidents where the number affected was unknown or undisclosed.
11/16/2016 700,000,000 IoT/Phones?
Yesterday Kryptowire identified several models of Android firmware which collected user personal data and transmitted that without disclosure or consent using Firmware Over The Air (FOTA) update software managed by Shanghai Adups Technology Co. Ltd. (ADUPS). ADUPS claims 700 million devices under management. The smart phones are lower cost devices where users accept advertising in exchange for the lower rates. They are available through major on line retailers.
Compromised information included user identification, device information, complete text messages, contact lists, call history, full telephone numbers, unique device identifiers including the International Mobile Subscriber Identity (IMSI) and the International Mobile Equipment Identity (IMEI). The same firmware can bypass the Android permission model to execute remote commands with system privileges, thus be able to remotely reprogram the devices. The ability to remote control so many devices without user knowledge or consent makes the power of a distributed denial of service (DDOS) attack more powerful than ever before.
Know that his is NOT a bug. ADUPS designed the software to help a Chinese phone manufacturer monitor user behavior, According to ADUPS that version of the software was not intended for American phones. For technically oriented material see KrebsOnSecurity. For a more general description see NY Times.
[ Intended or not this compromise spread. How long has it been monitoring us? -ed ]
In addition to sources cited above the Chronology of Data Base Breaches maintained by the Privacy Rights Clearinghouse was used. Their website is a valuable resource for those seeking information on basic privacy, identity theft, medical privacy and much more. They are highly recommended as are The Identity Theft Resource Center (ITRC).
2016 Compromises affecting 10,000 or more
2016 Compromises affecting less than 10,000
2016 Summary of Compromises
2016 General Information
Return to References page
Return to Year links page
Links above were active at the time they were gathered. Links shown in non-hypertext (not clickable) are known to be no longer supported on their hosts.