June 30, 2016 10 million more health care records available for purchase. Story Tweet
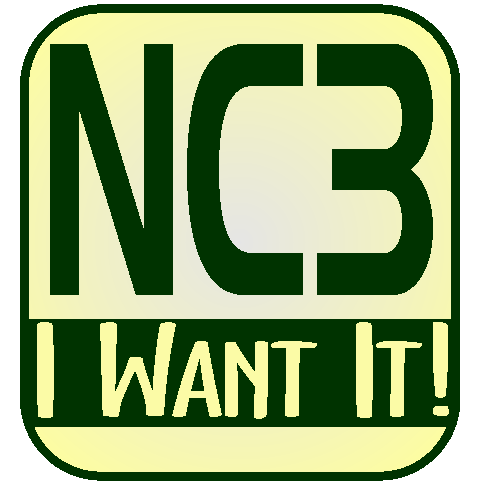
June 30, 2016  In Virginia there is no longer an expectation of privacy for your internet connected computer. According to the judge, law enforcement does not even require a warrant. Story Tweet
In Virginia there is no longer an expectation of privacy for your internet connected computer. According to the judge, law enforcement does not even require a warrant. Story Tweet
June 30, 2016 Noodles reveals 25+ stores compromised, but not how many. Also fudges some dates as to when they knew about it. This Update Start of the Story Tweet
June 30, 2016 Security software should be, well, secure, right? Turns out, not so much and worse, as Symantec was was told. Story Tweet
June 29, 2016 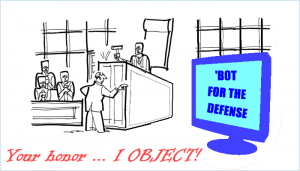 A chatbot has guided people in over a quarter million cases for appealing parking tickets with a face value of $4M. It has been 64% successful. The 19-year old inventor charges nothing for this service and is working on expansion. Story Tweet
A chatbot has guided people in over a quarter million cases for appealing parking tickets with a face value of $4M. It has been 64% successful. The 19-year old inventor charges nothing for this service and is working on expansion. Story Tweet
June 29, 2016 FaceBook privacy notice was a hoax. Story Tweet
June 29, 2016 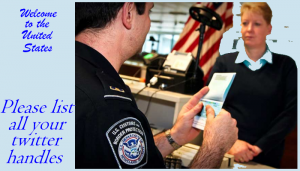 Be prepared to reveal your social media accounts to Customs when you are entering the United States. New regulations up for review to burden the lawful. Will crooks bother? Is there going to be a “Department of Blog Review”? What will that cost the taxpayers?
Be prepared to reveal your social media accounts to Customs when you are entering the United States. New regulations up for review to burden the lawful. Will crooks bother? Is there going to be a “Department of Blog Review”? What will that cost the taxpayers?
Story Tweet
June 29, 2016  Forced installation of Windows10 rendered computers non operable. Customer support was no help. David sued Goliath and won. Story Tweet
Forced installation of Windows10 rendered computers non operable. Customer support was no help. David sued Goliath and won. Story Tweet
June 29, 2016 2.2 million terrorist suspects or other persons of interest were exposed in an on-line database with zero cybersecurity. Story Tweet
June 28, 2016  BrExit complicates US-UK-EU privacy rule compliance. EU privacy rules are strictest, and if UK wants access to common market, they must comply. This Update Start of the Story Tweet
BrExit complicates US-UK-EU privacy rule compliance. EU privacy rules are strictest, and if UK wants access to common market, they must comply. This Update Start of the Story Tweet
June 28, 2016 US & EU reach agreement on new privacy rules ending 15-year “Safe Harbour” agreement. This Update Start of the Story Tweet
June 28, 2016  Tools for living free in a surveillance state are moving into the mainstream. Here are a few. Story Tweet
Tools for living free in a surveillance state are moving into the mainstream. Here are a few. Story Tweet
June 28, 2016 How technology collecting information by accident turned us into a surveillance state. Hint: follow the money. Story Tweet
June 27, 2016  IRS hacked again, abruptly ends IP-PIN access. How many exposed this time? They either don’t know or are not saying. Story Tweet
IRS hacked again, abruptly ends IP-PIN access. How many exposed this time? They either don’t know or are not saying. Story Tweet
June 27, 2016 Having developed a good habit of examining ATM machines a researcher on vacation found a skimmer. Chance favors the prepared! Story Tweet
June 25, 2016 The FBI says it can de-anonymize Tor users and wanted to classify even its reasons for withholding the exploit citing “national security”. The exploit is part of over 1,000 cases, but how can an unexplained exploit stand cross examination as provided by the Confrontation Clause of the Sixth Amendment? Story Tweet
June 24, 2016 Multiple Uber Oops. Flaws in the smartphone app and web site expose free ride codes and driver information. Report it? Multiple people did over several months. Uber’s response “We won’t fix it. Out of Scope”. Story Tweet
June 23, 2016 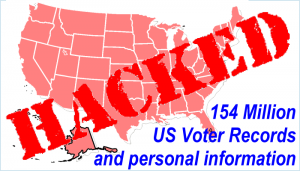 A legally sold database containing voter records matched with considerable personally identifiable information (PII) was found on rented cloud space with absolutely zero cybersecurity. The original seller of the data was identified, they identified who they sold it to, and that company said they had been hacked. Are we unhappy yet? Story Tweet
A legally sold database containing voter records matched with considerable personally identifiable information (PII) was found on rented cloud space with absolutely zero cybersecurity. The original seller of the data was identified, they identified who they sold it to, and that company said they had been hacked. Are we unhappy yet? Story Tweet
June 23, 2016  Ransomware on the rise despite improvements in cybersecurity. Story Tweet
Ransomware on the rise despite improvements in cybersecurity. Story Tweet
June 23, 2016 Apple Airport routers get security update, but the reasons for that update are unclear. One explanation indicates a DNS booby trap vulnerability. Story Tweet
June 23, 2016 When is a stopwatch app more than a stopwatch app? When it contains malware that can make calls, block texts and steal your information. Story Tweet
June 23, 2016 How do I hack thee? Let me count the ways. Top Eight Exploits used to highlight 21 vulnerabilities allowing browser code to elevate privileges to the highest level and make your smartphone their device to control. Story Tweet
June 23, 2016 Why risk getting your picture taken when you insert an ATM skimmer or a shimmer? Hack at long distance to perform a cash out at $20,000 in 15 minutes? Story Tweet
June 23, 2016 T-Mobile employee takes 1.5 million customer records to sell. Story Tweet
June 23, 2016 Citrix GoToMyPC hit with attack using recycled passwords. Password reset was applied to all users. Story Tweet
June 22, 2016  Started in March 2016, the Pentagon’s HackMe program has resulted in 138 disclosed vulnerabilities, up from previous number. Secretary of Defense calls it a “cost effective” program with over 1,000 white hat hackers participating. This Update Start of the Story Tweet
Started in March 2016, the Pentagon’s HackMe program has resulted in 138 disclosed vulnerabilities, up from previous number. Secretary of Defense calls it a “cost effective” program with over 1,000 white hat hackers participating. This Update Start of the Story Tweet
June 22, 2016  Update: Reason invades the Senate, by one or two votes depending on how you count. The “little typo fix” slipped into an appropriations bill that would have expanded surveillance without a warrant was defeated. It may be brought up again, and again, and again. Is this why we elected Senators? This Update Start of the Story Tweet
Update: Reason invades the Senate, by one or two votes depending on how you count. The “little typo fix” slipped into an appropriations bill that would have expanded surveillance without a warrant was defeated. It may be brought up again, and again, and again. Is this why we elected Senators? This Update Start of the Story Tweet
June 22, 2016 The Clinton Foundation was hacked and the release of documents good, bad, ugly and embarrassing are expected. Story Tweet
June 19, 2016 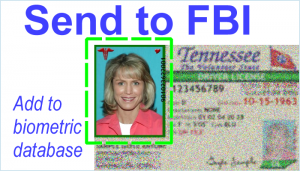 Criminal, civilian, visa applicant, or just someone with a driver’s license, the FBI’s Next Generation Identification-Interstate Photo System (NGI-IPS) with over 400 million images knows you now, or will soon. Is it used properly? Does it ensnare false positives (innocents) for investigation? No one knows. The program is 5+ years behind on “mandatory” public disclosures and never been audited per GAO report issued just four days ago. This Story. Apple sharing fingerprints with the NSA, TSA scans building body biometric database, changes in civil rules of procedure violating the 4th Amendment and more
Criminal, civilian, visa applicant, or just someone with a driver’s license, the FBI’s Next Generation Identification-Interstate Photo System (NGI-IPS) with over 400 million images knows you now, or will soon. Is it used properly? Does it ensnare false positives (innocents) for investigation? No one knows. The program is 5+ years behind on “mandatory” public disclosures and never been audited per GAO report issued just four days ago. This Story. Apple sharing fingerprints with the NSA, TSA scans building body biometric database, changes in civil rules of procedure violating the 4th Amendment and more
start here. Tweet
June 18, 2016  Acer store hacked, exposes charge card information on users over the last year. Story Tweet
Acer store hacked, exposes charge card information on users over the last year. Story Tweet
June 17, 2016  Ether, an experimental cryptocurrency raised over $150 million in crowdfunding. $50 million was “moved”. A paper described multiple weaknesses foretold the compromise. Story Tweet
Ether, an experimental cryptocurrency raised over $150 million in crowdfunding. $50 million was “moved”. A paper described multiple weaknesses foretold the compromise. Story Tweet
June 16, 2016  Marketing company hacked exposing 42 million users of many automotive, pets, sports, tractor, and other domains. Story Tweet
Marketing company hacked exposing 42 million users of many automotive, pets, sports, tractor, and other domains. Story Tweet
June 16, 2016 DraftKings / FanDuel looking to merge amid their legal problems and declining market value. There are benefits. This Update Start of the Story Tweet
June 16, 2016  Card skimmers at ATMs and gas pumps are thinner, being inserted deeper and faster than ever before. Get in the habit of covering your PIN. Story Tweet
Card skimmers at ATMs and gas pumps are thinner, being inserted deeper and faster than ever before. Get in the habit of covering your PIN. Story Tweet
June 15, 2016 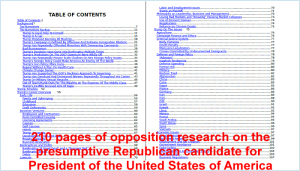 Opposition Research on the presumptive Republican candidate was placed on line. Maybe grab a copy of the 210 page PDF before it is disappeared. Story Tweet
Opposition Research on the presumptive Republican candidate was placed on line. Maybe grab a copy of the 210 page PDF before it is disappeared. Story Tweet
June 14, 2016 Is broadband internet a utility subject to regulations such as net neutrality? In a victory for consumers the US Court of Appeals today said YES.
Story Tweet
June 14, 2016  Texas Department of Transportation traffic notification displays hacked to show other messages. Story Tweet
Texas Department of Transportation traffic notification displays hacked to show other messages. Story Tweet
June 14, 2016 Greenwich University / UK hacked exposing personal information on over 21,000 students, staff and faculty. Story Tweet
June 14, 2016 Russia hacks DNC gets Trump file. Story Tweet
June 14, 2016 Email notifications from a company, generally routine, until one system hiccup so each new notification added a CC of all previous addressees. Story Tweet
June 14, 2016 North Korea has hacked South Korea for years exposing 140,000 computers in 160 companies and government agencies. Story Tweet
June 13, 2016  If a lobbyist ghostwrites a bill for the Legislative Branch, that bill has some elected official’s name on it and there will be at least two votes and a presidential signature. If the Supreme Court adds powers not granted by Congress there is no elected official’s name on it, not one vote and no presidential signature. Who makes law in this country? Per Article I, Section I US Constitution: the Legislative Branch, not the Judicial. So how are the proposed changes to Rule 41 of the Federal Rules of Criminal Procedure going to become law? Congress just has to do … nothing. Then new surveillance rules that may violate the Fourth Amendment, impose US laws on the world (allowing them to do the same to US), scrapping victim privacy, allow multi-district venue shopping, and more just “poof” becomes law. The largest increase in surveillance power is flying under the public radar. Story Tweet1 Tweet2 Tweet3 Tweet4
If a lobbyist ghostwrites a bill for the Legislative Branch, that bill has some elected official’s name on it and there will be at least two votes and a presidential signature. If the Supreme Court adds powers not granted by Congress there is no elected official’s name on it, not one vote and no presidential signature. Who makes law in this country? Per Article I, Section I US Constitution: the Legislative Branch, not the Judicial. So how are the proposed changes to Rule 41 of the Federal Rules of Criminal Procedure going to become law? Congress just has to do … nothing. Then new surveillance rules that may violate the Fourth Amendment, impose US laws on the world (allowing them to do the same to US), scrapping victim privacy, allow multi-district venue shopping, and more just “poof” becomes law. The largest increase in surveillance power is flying under the public radar. Story Tweet1 Tweet2 Tweet3 Tweet4
June 13, 2016 51 million iMesh accounts exposed. Did you recycle a user ID and/or password? Time to stop that practice and change them now. Story Tweet
June 12, 2016  Wisconsin, American’s Dairy Land, home to the Green Bay Packers, land of bratwurst, beer, cheese, cranberries, whey, ginseng root, sweet corn, 16,000+ lakes, and a cyber launching pad for China. Oh, yes it is. Story Tweet
Wisconsin, American’s Dairy Land, home to the Green Bay Packers, land of bratwurst, beer, cheese, cranberries, whey, ginseng root, sweet corn, 16,000+ lakes, and a cyber launching pad for China. Oh, yes it is. Story Tweet
June 11, 2016 Those bank heists via the SWIFT system, maybe it wasn’t North Korea? Another perpetrator proposed. This Update Start of Story Tweet
At 1.374 billion accounts compromised 2014 was the worst year since we started tracking in 2005. As of 6/9/2016, with the reports to date (less than half a year) over 1.415 billion accounts have been compromised. No celebration to be had, this is just bad news. Cops are leaking data, crooks are leaking data, companies … data is leaking all around and exposing us all to financial crimes and identity theft. In too many places cybersecurity is just a word.
June 10, 2016  Domains that look like they belong to Apple are designed to obtain user credentials. Over 200 found. Story Tweet
Domains that look like they belong to Apple are designed to obtain user credentials. Over 200 found. Story Tweet
June 10, 2016 uTorrent accounts exposed by hosting vendor. Story Tweet
June 10, 2016  Update to the 2014 Home Depot exposure of 56 million charge accounts. They actively avoided solutions since 2008 creating a risk to their duty of protection. Judge declines to dismiss case. This Update Start of the Story Tweet
Update to the 2014 Home Depot exposure of 56 million charge accounts. They actively avoided solutions since 2008 creating a risk to their duty of protection. Judge declines to dismiss case. This Update Start of the Story Tweet
June 9, 2016  The number of Wendy’s restaurants with malware discovered in January is looking to be a lot bigger than the 300 reported. This Update Start of the Story Tweet
The number of Wendy’s restaurants with malware discovered in January is looking to be a lot bigger than the 300 reported. This Update Start of the Story Tweet
June 9, 2016 Almost 300,000 records with name, address and more found for sale on DarkNet. Asking price: $USD 12 Billion, obo, BitCoin only. The data came from where? Story Tweet
June 9, 2016 VK.COM with over 300 million users hacked exposing 100 million records including plain text passwords. Story Tweet
June 9, 2016 Good neighbor State Farm gave our data to a marketing firm in another country who put production data in a development system that got hacked. Thanks good neighbor! Story Tweet
June 9, 2016  Hackers hacked. Karma bites crooks. Story Tweet
Hackers hacked. Karma bites crooks. Story Tweet
June 8, 2016 Botnet found CiCiPOS.exe as part of capturing 1+million charge cards from multiple restaurants, hotels, theaters and more. This Update Start of the Story Tweet
June 8, 2016 Universities hit with ransomware. Some prepared. Some not.
Story Tweet
June 7, 2016 Update to CiCi’s Pizza hack. TeamViewer says it wasn’t hacked but is investigating possibly re-used credentials exposed in other breaches. This Update Start of the Story Tweet
June 7, 2016 Malware Angler variant beats Microsoft’s best EMET security. Story Tweet
June 7, 2016 Ad sellers are going to the FTC to stop AdBlockers, those things that protect us from malware delivered via advertising. Oh yes, its true. Story Tweet
June 6, 1944 – 72 years ago the invasion of “Fortress Europe”, starting the last phases of World War II, commenced with history’s largest assault by forces deployed by air and sea against Normandy, France. Victory in Europe (V-E Day) would follow eleven months later on May 8, 1945.
June 6, 2016 Bank heists via SWIFT linked to North Korea. This Update Beginning of the Story Tweet
June 6, 2016 Cybersecurity breaches at US Federal Reserve exposed via Freedom Of Information. Problems at 12 branches remain “undisclosed”. This Update Beginning of the Story Tweet
June 6, 2016 35 Bangladesh SWIFT transfers were rejected by NY Fed, then some were approved. Were warning signs missed? This Update Beginning of the Story Tweet
June 6, 2016  Panama Papers: Several detailed examples of tangled webs created by a Panamanian firm to help US citizens avoid, or evade, US tax laws. This Update Start of the Story Tweet
Panama Papers: Several detailed examples of tangled webs created by a Panamanian firm to help US citizens avoid, or evade, US tax laws. This Update Start of the Story Tweet
June 6, 2016 Were hacked TeamViewer credentials used to hack CiCi’s Pizza? Lots of maybe in there, but one thing is certain. If you use TeamViewer: change your password This Update Start of the Story Tweet
June 6, 2016 Six years after Dr. Kohno demonstrated cars could be hacked Mitsubishi put 100,000 PHEV into customer hands with similar vulnerabilities. Story Tweet
June 6, 2016 VISA is testing a prototype payment ring at the Summer Games in Rio De Janeiro, Brazil. Despite the marketing claims Samy Kamkar made one in 2015 and that one you can load with whatever charge card information you have. Story Tweet
June 5, 2016  Charge cards used at CiCi’s Pizza turning up at the center in patterns of fraud. Banks turn to Brian Krebs who finds few at CiCi’s want to talk to him and that this hack may have been due to other hacks. Will we ever find out how many were compromised? Will companies protect our data? An eWeek article says no. Story Tweet
Charge cards used at CiCi’s Pizza turning up at the center in patterns of fraud. Banks turn to Brian Krebs who finds few at CiCi’s want to talk to him and that this hack may have been due to other hacks. Will we ever find out how many were compromised? Will companies protect our data? An eWeek article says no. Story Tweet
June 4, 2016 May summaries are complete. The 2016 summary has the numbers, percentages and more. There were 66 incidents with an unknown, or undisclosed number compromised. There were 25 incidents where under 56,082 were compromised. There were ten large exposures of over 10,000 each. They were:
Ohio Department of Mental Health (59,000),
FDIC (10,000),
Mayfield Clinic of Cincinnati OH (23,341),
National Counseling Group VA (23,000),
Medical Colleagues of Texas (68,631),
California Correctional Health Care (400,000),
Poway Unified School District CA (36,000),
San Juan County NM (12,000),
Southeast Eye Institute, PA (87,314).
June 3, 2016  36 million exposed from 110 sites because of poor security practices using popular MongoDB software. Story Tweet
36 million exposed from 110 sites because of poor security practices using popular MongoDB software. Story Tweet
June 2, 2016 Did a major utility have no security on 47,000 of their computers and servers? If so, were they vulnerable to the same hack that put over a million residents of Ukraine in the dark? Story Tweet
June 2, 2016 NFL trainer’s backpack and laptop exposed thousands of NFL players medical history since 2004. Incredibly HIPAA may not apply because the NFL isn’t a covered entity, but the exposure is the same. Story Tweet
June 2, 2016 Why PayPal might decide not to deliver to you at all. Story Tweet
June 2, 2016 Difference resolution promised in a court of law can get moved to arbitration and a court of something else completely. How? Story Tweet
June 1, 2016  Riding herd on hundreds of millions of exposed internet credentials is a huge white hat and all ’round nice guy Troy Hunt. Why you should give his web site your email address. Story Tweet
Riding herd on hundreds of millions of exposed internet credentials is a huge white hat and all ’round nice guy Troy Hunt. Why you should give his web site your email address. Story Tweet
June 1, 2016 Theranos, a media darling, “recalled” two years of medical test results. A week later a suit seeking class action certification. A day later, another such suit. Today, the founder’s value in the company was changed to zero from $4.5 billion dollars and a first place in a Forbes list. How did it go two years without FDA certifications? Turns out there is a loophole that Congress is in no hurry to close, despite multiple other companies offering un-proven medical tests. First Class Action Second Class Action Founder Value = Zero & The Loophole Start of the Story Tweet